Now Reading: Blue-Green vs Canary Deployments: Release Strategies
-
01
Blue-Green vs Canary Deployments: Release Strategies
Blue-Green vs Canary Deployments: Release Strategies
Overview of Release Strategies
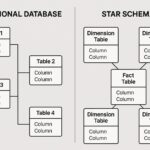
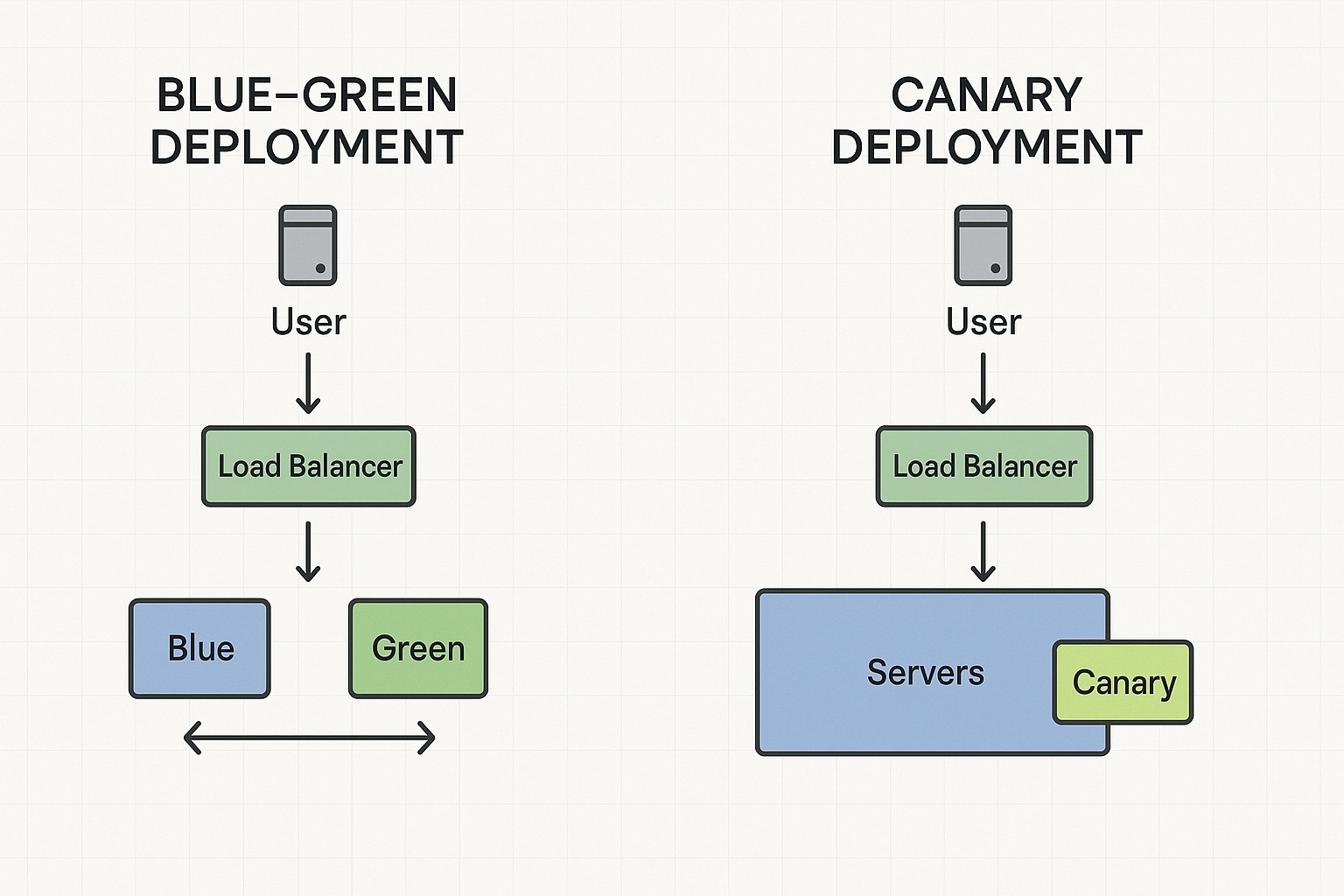
Organizations delivering software frequently face the challenge of updating features, fixing defects, and maintaining uptime. Two deployment paradigms commonly used to balance speed and safety are blue-green deployment and canary deployment. Blue-green creates two production environments that are functionally identical; traffic is switched between them to make updates appear instantaneous to users. Canary deployments release new software to a small portion of the user base or infrastructure first, observe performance, and gradually expand the exposure.
Choosing between these approaches depends on factors such as the architecture of the system, data migration responsibilities, regulatory constraints, and the organization’s appetite for risk. Blue-green offers an almost instantaneous rollback by flipping traffic back to the previous environment, but it demands duplicate production environments and robust data synchronization. Canary reduces blast radius and enables real-time learning from live traffic, yet it hinges on mature observability, robust feature flags, and careful ramp control to avoid customer-visible incidents.
- Blue-green vs Canary definitions: blue-green uses two full production environments with a single switch; canary exposes the new version gradually to a subset of users or infrastructure.
- Readiness prerequisites: blue-green requires identical idle/active environments and reliable routing; canary requires instrumentation, feature flags, and staged exposure controls.
- Risk management: blue-green provides a fast rollback but higher upfront infrastructure cost; canary reduces risk incrementally but depends on telemetry and threshold-based decisioning.
- Pitfalls to avoid: data synchronization in blue-green and misconfigured exposure in canary can both undermine release quality.
Blue-Green Deployment in Practice
In a blue-green setup, teams maintain two production ecosystems, often named blue and green. The active environment runs the current release while the idle environment is prepared with the next version. Once the green environment is validated in isolation and via internal checks, traffic is redirected from blue to green using a load balancer, DNS failover, or service mesh routing. The old version remains ready to serve as an immediate fallback, ensuring near-zero recovery time objective if a rollback is required. Database changes require careful planning to avoid divergence; backward-compatible migrations or dual-write strategies are commonly used to maintain data consistency across environments.
Key operational steps include synchronizing configuration and secrets between environments, running automated smoke tests, validating critical business flows, and monitoring latency, error rates, and availability during and after the switch. The governance model should specify criteria for proceeding with the switch, exit criteria in case of failures, and a sunset plan for decommissioning the old environment. Because the switch can be instantaneous, teams frequently pair blue-green with canary techniques for risky features or migrations.
- Prepare and synchronize environments to ensure parity in runtime, configuration, and data considerations.
- Deploy the new version to the idle (green) environment and perform automated validation in isolation.
- Run smoke tests and health checks, validating critical paths and back-compatibility concerns.
- Shift production traffic to the new environment and monitor real-time metrics for a defined window.
- Confirm stability, retire the old environment, and establish a rollback plan if stability degrades.
Canary Deployments in Practice
Canary deployments introduce the new version to a small slice of users or servers and monitor its behavior under real load. The exposure is gradually increased as telemetry confirms that latency, error rates, and business signals meet expected thresholds. By tying exposure to measurable goals, canaries reduce the risk of widespread outages while allowing faster iteration on customer-visible features. Feature flags are commonly used to decouple release from deployment, enabling rapid disablement if issues arise.
Effective canary programs rely on granular instrumentation, robust alerting, and a disciplined ramp strategy. Teams define success criteria, such as acceptable percent change in key metrics over a defined window, and implement automatic halts if thresholds are breached. The organizational readiness to respond—rapid rollback, hotfix channels, and clear ownership—significantly influences outcomes more than the mere technical setup.
- Canary ramp plan: decide initial exposure and ramp-up pace (e.g., 1-5%, region-based, or user-segment-based).
- Telemetry and thresholds: define latency, error rate, saturation, and business metrics thresholds for progression or halt.
- Rollback protocol: specify how to halt exposure, revert routing, and redeploy previous versions if issues arise.
- Coordination and communication: ensure clear ownership, incident runbooks, and timely stakeholder updates during the rollout.
Decision framework: When to choose Blue-Green or Canary
Deciding on blue-green or canary comes down to the nature of the change and the system’s risk tolerance. If a release involves breaking database migrations, long downtimes, or stringent regulatory confirmation cycles, blue-green can provide a safer, more controllable path with a defined cutover. If the product team seeks rapid feedback, strong feature flag governance, and the ability to test in production with minimal user impact, canary deployments are attractive. Many organizations also blend the approaches: use blue-green for major releases or high-risk migrations, and apply canary for smaller incremental features or infrastructure changes.
Practical guidelines include mapping deployment risk to exposure strategy, defining clear success and rollback criteria, and ensuring the organization has the telemetry, automation, and incident response processes to support either approach. The decision is rarely binary; it is a spectrum shaped by the system architecture, the customer base, and the maturity of the observability and CI/CD tooling.
Operational Considerations and Automation
Automation underpins reliable blue-green and canary deployments. Infrastructure as code, immutable environments, and repeatable pipelines help eliminate drift between environments and reduce manual errors. In cloud-native stacks, integration with load balancers, service meshes, and feature flag platforms enables precise routing and quick rollback. Observability is not a luxury but a prerequisite: teams instrument end-to-end SLOs, capture real-time dashboards, and establish alerting that can automatically pause a rollout if issues are detected.
Security and compliance require attention during releases as well. Secrets management, access controls, and audit trails must persist across both active and idle environments; migration strategies should maintain data integrity and consistency. Teams should also plan for cost implications, as running parallel production environments increases spend; optimization should focus on turning off or decommissioning the idle environment promptly once release stability is confirmed.
Risk, Rollback, and Compliance
Beyond technical readiness, releases must align with risk management and regulatory requirements. Clear rollback procedures, time-bound decision windows, and automated monitoring reduce the mean time to recover. For industries with strict data sovereignty or privacy constraints, blue-green can help isolate changes in a controlled environment, while canaries can provide real-time insight with rigorous telemetry and sampling practices to ensure no policy violations are introduced.
Documentation and auditability matter as much as code. Change logs, release notes, and automated evidence of testing and approvals should be accessible to stakeholders and auditors. In distributed teams, consistent runbooks and incident response playbooks define who can authorize a switch and how post-release reviews are conducted. Finally, cost management should be part of the governance model because maintaining two parallel production footprints has financial implications.
Implementation Patterns and Governance
Teams commonly implement blue-green and canary patterns using a combination of infrastructure automation, configuration as code, and deployment automation. In Kubernetes, this can involve separate deployments and a single service with a dynamic label selector, while service meshes provide fine-grained traffic routing and percentage-based traffic shifts. For feature flags, a central flag management system allows enabling or disabling capabilities without redeploying. The governance layer should specify who can initiate cutovers, what thresholds trigger automatic halts, and how post-release reviews are conducted.
# Example: quick blue-green switch using a hypothetical routing tool
# Build and deploy the new version to the idle environment
deploy --env green --version 2.1.0
# Run smoke tests
run-smoke --env green
# Switch traffic from blue to green
route --from blue --to green
# Validate production behavior, then decommission blue after verification
wait-for-stability --env green
decommission --env blue --retain-archivesFAQ
What is the primary difference between blue-green and canary deployments?
Blue-green deploys rely on two full production environments and a single switch that routes all traffic to the new version, offering a quick revert by flipping back. Canary deploys introduce the new version to a small, controlled subset of users or infrastructure and progressively increases exposure as confidence grows, reducing risk through gradual rollout and telemetry-driven decisions.
How should I measure success for a release?
Success is defined by a combination of technical and business metrics, including latency, error rates, saturation, and confidence in service level objectives, as well as user impact indicators such as conversion or retention. A well-designed release uses automated checks, real-time dashboards, and a pre-defined rollback plan if any metric deviates beyond thresholds.
What kinds of systems are best suited for blue-green versus canary?
Blue-green is well-suited to systems requiring clean, instant cutovers and strong isolation between old and new versions, particularly when data migrations can be made backward-compatible. Canary excels in complex, high-velocity environments where continuous delivery and rapid feedback are valued, and where feature flags and granular telemetry can manage staged exposure.
Can these strategies be combined?
Yes. Organizations commonly use blue-green for major version releases or migrations that require strong rollback guarantees, and canary for incremental feature delivery or infrastructure updates. A blended approach lets teams get the safety of a controlled cutover while still getting live feedback for smaller changes.
What are common pitfalls?
Common issues include underestimating data synchronization complexity in blue-green, over- or under-fueling the exposure in canaries due to poor thresholds, failing to instrument or alert adequately, and neglecting to plan decommissioning of idle environments, which can incur unnecessary costs.