Why employee cybersecurity training matters Organizations increasingly rely on digital systems for operations, customer data, and complex supply chains. Yet the most common breach vectors remain rooted in human factors—employees
Cybersecurity
Discover expert insights and practical guides in Cybersecurity. Learn key trends, tools, and strategies to improve your skills and drive business results.
Introduction: The move toward passwordless authentication Across many industries, organizations are prioritizing security architecture that reduces reliance on static passwords. The push toward passwordless authentication is driven by the recognition
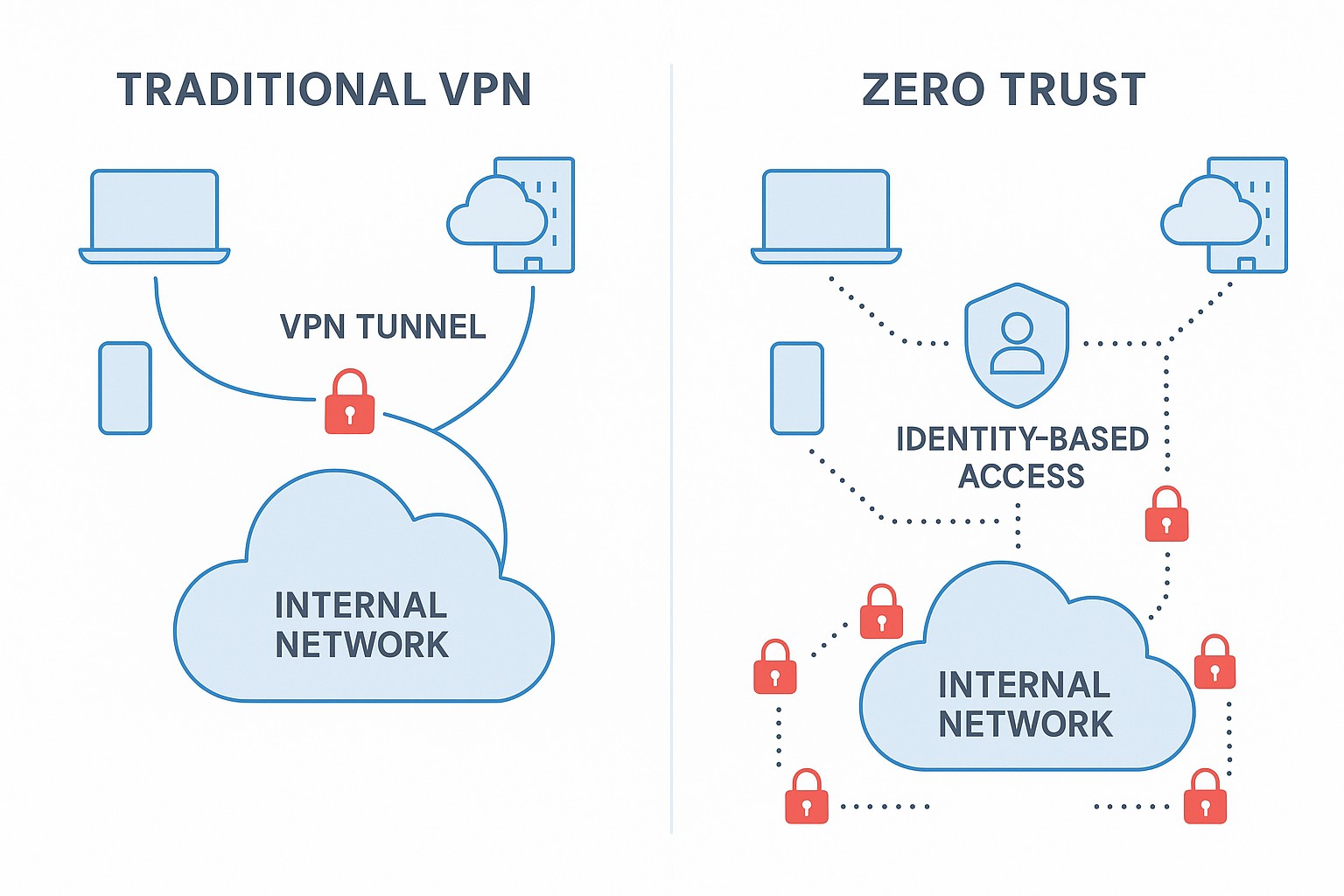
Understanding VPN-based remote access Traditional VPN-based remote access was designed to extend a trusted corporate perimeter to users outside the office. In this model, employees, contractors, and partners connect through
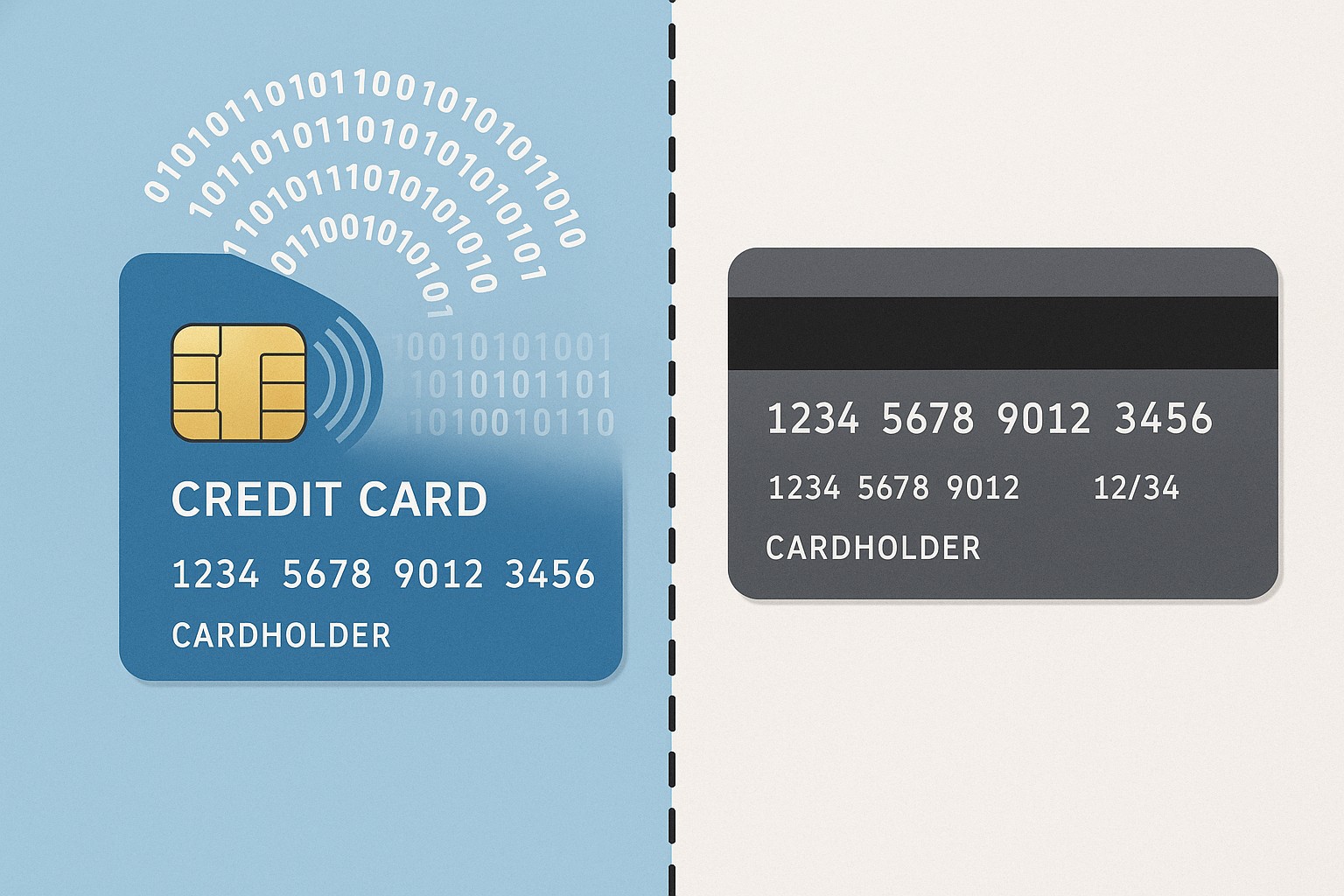
Overview of EMV and Magnetic Stripe Technologies EMV chip cards, short for Europay, MasterCard, and Visa, embed a microprocessor chip that stores payment credentials and performs cryptographic operations at the
Overview of Red Teams and Blue Teams Red Teams and Blue Teams are complementary forces within an organization’s cybersecurity program. The Red Team plays the role of an adversary, employing
Understanding the Shared Responsibility Model In cloud deployments, responsibility for security is divided between the cloud provider and the customer. The provider secures the underlying infrastructure—physical data centers, hardware, network
Overview: Data Privacy vs Data Security In modern enterprises, data is both an asset and a potential liability. Data privacy and data security operate in tandem to protect people and