Now Reading: IPv4 vs IPv6: Internet Protocols and Transition
-
01
IPv4 vs IPv6: Internet Protocols and Transition
IPv4 vs IPv6: Internet Protocols and Transition
Overview of IPv4 and IPv6
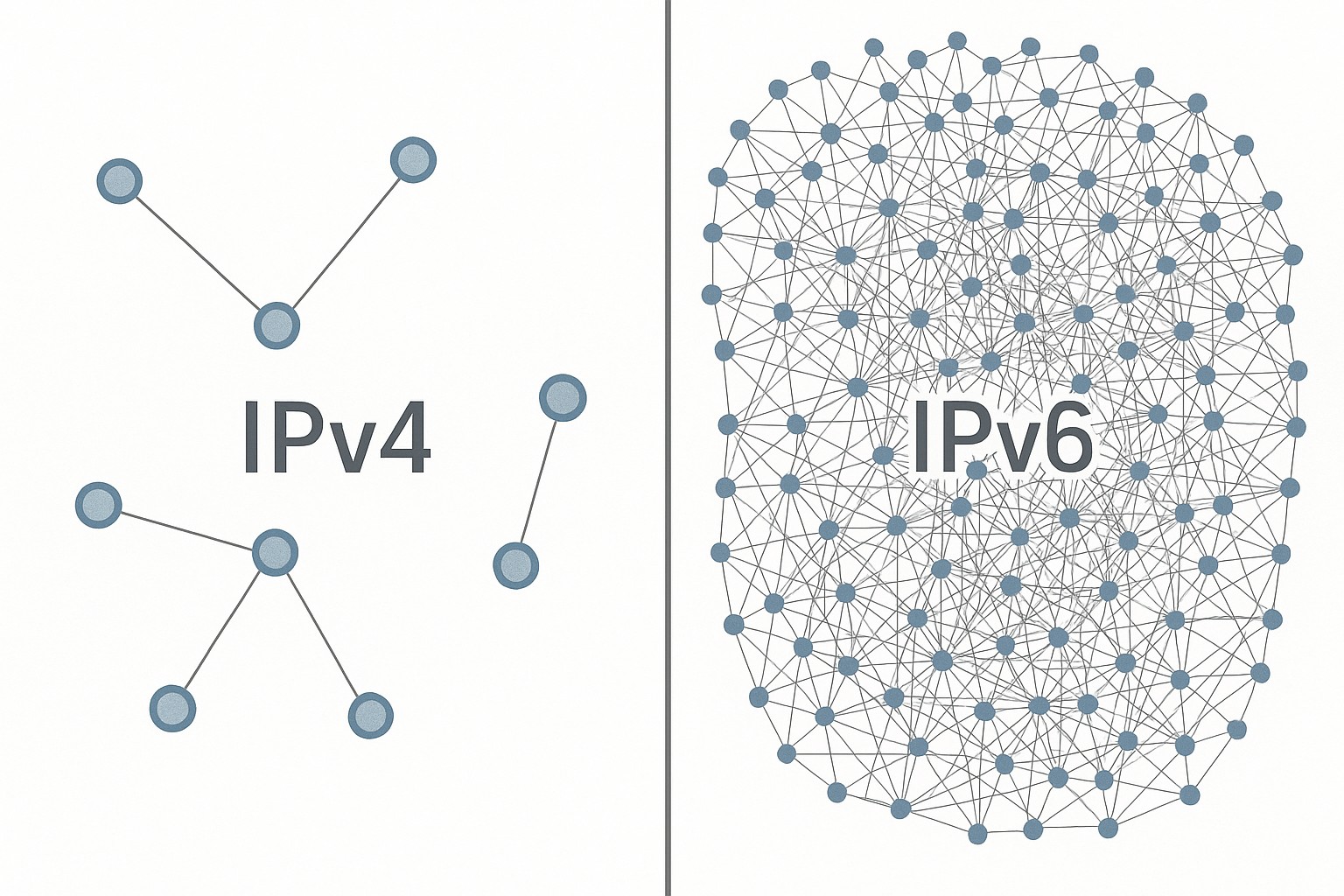
IPv4 has underpinned the growth of the Internet since the early 1980s, delivering a straightforward 32‑bit addressing scheme that supports roughly 4.29 billion unique addresses. As global connectivity surged across enterprises, mobile devices, and the Internet of Things, the limitations of that fixed space became increasingly apparent. Address allocation practices, uneven distribution, and the natural inefficiencies of subnetting in large networks drove address exhaustion to the forefront of planning discussions. To adapt, the industry deployed a suite of techniques—most notably Network Address Translation (NAT)—to extend the usable life of IPv4, enabling many devices to share a smaller pool of public addresses while preserving outward connectivity. However, NAT also introduced complexity, broke end‑to‑end connectivity in some applications, and complicated certain protocols and security models that rely on direct addressing.
IPv6 was designed to address these fundamental constraints with a vastly larger address space and architectural refinements. The 128‑bit space of IPv6 provides an effectively inexhaustible pool of global addresses, enabling scalable subnets and easier, more deterministic addressing models for devices, services, and infrastructure. Beyond size, IPv6 incorporates improvements in autoconfiguration, routing efficiency, and the separation of local versus global scopes, which reduces the administrative burden of large networks. Stateless Address Autoconfiguration (SLAAC) and DHCPv6 offer complementary approaches to provisioning address information, while the revised header format supports faster packet processing in routers and endpoints. Although IPsec is associated historically with IPv6 and is available in practice, security success still hinges on deliberate configuration, policy design, and operational discipline rather than the protocol alone.
Transitioning to IPv6 has been and remains a staged process. In most environments, dual‑stack deployments—where IPv4 and IPv6 run in parallel—form the backbone of contemporary networks, allowing gradual migration without disrupting existing services. A mix of bridging technologies, translation layers, and careful routing design supports coexistence with IPv4 as organizations modernize their infrastructure, data centers, and edge devices. Regional differences in policy, vendor readiness, and peering architectures mean that progress is uneven by geography and sector, with some industries advancing rapidly and others waiting on legacy systems, tooling, or customer requirements. The result is a pragmatic, multi‑year evolution rather than a single leap from IPv4 to IPv6.
Addressing and Namespace
At the core of IPv4 versus IPv6 is the question of address space and how networks organize those addresses into prefixes, routes, and identities. IPv4’s 32‑bit space supports roughly 4.29 billion addresses, a number that proved insufficient as devices proliferated and address blocks were subdivided for organizational needs. IPv6 expands this dramatically to 2^128 addresses, enabling an abundance of global prefixes, subnets, and end‑user devices while reducing the administrative overhead of address planning. The shift also aligns with contemporary network design practices that favor long‑lived, hierarchically aggregatable prefixes for more scalable routing and policy control.
In IPv4, private address spaces and NAT became foundational tools for conserving public addresses and enabling internal communication. IPv6 shifts toward global reachability by default, with private addressing (Unique Local Addresses) and link‑local addressing supporting intra‑site communication, automated configuration, and straightforward neighbor discovery. The IPv6 model also expands address types and scope definitions, introducing clear distinctions among link‑local, local, and global contexts and supporting modern privacy and security approaches that can be tuned through policy. Operators must also manage the implications of dual‑stack in which both address families coexist, including implications for routing tables, firewall rules, and monitoring that span both protocols.
- IPv4 address space: 4.29 billion possible addresses; widespread reliance on NAT to conserve space
- IPv6 address space: 2^128 addresses; abundant capacity for growth and more granular subnetting
- IPv6 subnetting and addressing: typical /64 subnets; support for SLAAC and DHCPv6; reduced dependence on NAT
- Naming and autoconfiguration: devices can configure themselves with minimal manual intervention in IPv6
Security and Privacy Considerations
Security design in IPv6 reflects a philosophy that emphasizes end‑to‑end reachability and modernized configuration mechanisms, but real‑world results depend on how networks are deployed and managed. IPsec remains a feature within IPv6, but it is not automatically deployed or guaranteed to protect all traffic. Organizations must plan for encryption, authentication, and integrity at the policy level, selecting appropriate mechanisms for each workload rather than assuming the protocol itself delivers stronger security by default. The private nature of some IPv6 features—such as privacy extensions that generate temporary addresses to limit device tracking—requires careful operational choices to balance privacy with observability, compliance, and troubleshooting.
As networks migrate, new surfaces of risk emerge. The Neighbor Discovery Protocol (NDP) and router advertisement messages create opportunities for spoofing or flooding attacks if not properly mitigated, and administrators should implement protections such as RA filtering, MLD snooping, and robust device hardening. Transition technologies—tunnels and translation layers that carry IPv6 traffic over IPv4—introduce additional considerations for security boundaries, logging, and access controls, since control planes and data planes can traverse multiple addressing realms. Thorough monitoring, anomaly detection, and consistent policy enforcement across IPv4 and IPv6 segments are essential to maintain a coherent security posture during the transition.
- Privacy extensions (RFC 4941) generate temporary addresses to reduce tracking; organizations must balance privacy with stable monitoring
- IPsec support is available in IPv6 but requires deliberate configuration and key management
- Neighbor Discovery Protocol threats (NDP spoofing, RA storms) necessitate protective measures (RA guard, MLD/ND filtering)
- Transition mechanisms (tunnels, NAT64/DNS64) can introduce risk surfaces if misconfigured or poorly monitored
Deployment and Transition Mechanisms
Organizations typically pursue a layered deployment strategy that leverages dual‑stack as the baseline while using transition tools to bridge legacy IPv4 resources and IPv6‑only infrastructures. Dual‑stack deployments preserve full compatibility with existing IPv4 services, enabling a controlled, incremental migration of applications, devices, and networks. They also require careful coordination of routing, firewall policies, and telemetry across both address families to avoid misconfigurations and performance issues. In parallel, deployment plans may leverage tunneling technologies to extend IPv6 connectivity across IPv4‑centric networks when immediate native IPv6 reachability is not feasible.
- Dual‑stack (IPv4 and IPv6 in parallel): maximizes compatibility and allows incremental migration but increases management overhead and potential misconfigurations
- Tunneling (6to4, Teredo, ISATAP, GRE, and similar approaches): provides IPv6 transport over existing IPv4 networks; suitable for temporary or constrained scenarios but can introduce latency and reliability concerns
- Translation (NAT64/DNS64): enables IPv6‑only networks to reach IPv4 services by translating addresses and protocols; useful where direct dual‑stack deployment is not possible but may affect end‑to‑end semantics
Beyond the technical options, successful transition requires governance, policy alignment, and operational readiness. Teams must define address planning standards, ensure consistent monitoring across stacks, and align security controls with the chosen path to IPv6. Early pilot programs focused on internal labs, regional data centers, or specific business units can reveal interoperability challenges, vendor support gaps, and educational needs before broad rollout. Moreover, service providers and peering partners play critical roles; coordinated migrations reduce the risk that partial adoption creates bottlenecks or performance anomalies at the network edge.
Economic and Operational Considerations
Adopting IPv6 is not solely a technical exercise; it is an operational and financial program. Initial costs often center on upgrading network gear, updating firmware and software, and training staff to design, deploy, and manage IPv6 environments. In many cases, devices already support IPv6, but configuration practices, monitoring tools, and security policies require updates. Long‑term returns include simpler address management at scale, more predictable routing, and improved capability to support new devices, services, and user experiences without contending with a shrinking IPv4 address pool. A structured transition plan helps organizations avoid the redundancy and risk of hasty migrations, enabling cost control and measurable milestones.
Operational considerations also include vendor readiness, support contracts, and the maturity of tooling for IPv6 monitoring, logging, and performance analysis. Enterprises should assess inventory, application dependencies, and service level requirements across both address families, ensuring that change management processes cover address allocation, firewall rules, DNS records, and security policies. The coordination with internet service providers, cloud platforms, and data center operators is essential for consistent behavior as prefixes are announced, routes propagate, and peering arrangements evolve to accommodate IPv6 traffic. A disciplined approach—grounded in governance, standardization, and ongoing education—helps ensure that the transition delivers resilience and value rather than disruption.
Future Outlook
Looking ahead, the trajectory of IPv6 adoption continues to accelerate in many sectors while remaining uneven in others. Regions with strong operator incentives, advanced content delivery networks, and proactive governance have moved toward wider IPv6 reach, enabling more direct end‑to‑end communication and reducing the long‑term reliance on NAT and translation mechanisms. At the same time, the persistent presence of IPv4 in consumer devices, enterprise applications, and legacy systems means that dual‑stack architectures will remain a core pattern for years to come. The continued focus on security, privacy, and performance will shape expectations for IPv6 deployments, with operators investing in autonomous on‑net provisioning, robust monitoring, and scalable policy frameworks.
As networks evolve to accommodate rapid growth in mobile, cloud, and edge computing, IPv6 will serve as a foundational enabler for scalable addressing, improved configurability, and more predictable routing. Enterprises that embrace IPv6 strategically—combining strong governance, phased pilot programs, and alignment with procurement and security standards—are well positioned to leverage new capabilities, support emerging architectures (such as IoT and 5G networks), and maintain a competitive edge through more agile service delivery. The overall takeaway is that IPv6 is not a “one‑time upgrade” but a long‑term evolution of how networks scale, secure, and enable modern digital services.
FAQ
What is the primary reason IPv6 was developed?
IPv6 was developed to address address exhaustion in IPv4 and to enable scalable, end‑to‑end connectivity with simpler configuration and improved routing efficiency. It provides a vastly larger address space, better support for autoconfiguration, and reorganized header fields that help networks scale as devices proliferate.
Will IPv6 replace IPv4 completely?
Most likely not in the near term. Dual‑stack deployments will continue for years, with IPv4 and IPv6 coexisting as organizations gradually transition. Some networks may rely on translation or tunneling methods to bridge IPv6‑only resources with IPv4 services, but a full, instantaneous switchover is unlikely due to legacy systems, applications, and vendor ecosystems.
What are the main transition mechanisms, and which to choose?
The main mechanisms are dual‑stack, tunneling, and translation. Dual‑stack runs both protocols in parallel and is the most common, maximizing compatibility but increasing management complexity. Tunneling carries IPv6 traffic over IPv4 networks to reach native IPv6 endpoints and is useful in limited scenarios but can affect performance. Translation (such as NAT64/DNS64) enables IPv6‑only networks to access IPv4 services by translating addresses and protocols, which can preserve interoperability but may impact end‑to‑end semantics for some applications.
What impact does IPv6 have on security and privacy?
IPv6 does not automatically guarantee stronger security; it provides more options and features that can improve privacy (such as temporary addresses) and security if properly configured. The move introduces new attack surfaces related to neighbor discovery, router advertisements, and transition mechanisms, so organizations must implement comprehensive protection, monitoring, and policy controls that span both IPv4 and IPv6 environments.
What should a business plan for IPv6 adoption include?
A solid plan should inventory assets and dependencies, define governance and policies, and establish a phased rollout with pilots, timelines, and measurable milestones. It should also address training for staff, vendor support, budgeting for upgrades, and a strategy for monitoring, security, and performance across IPv4 and IPv6 networks, ensuring alignment with service providers and cloud platforms.