Now Reading: Layer 1 vs Layer 2 Blockchain Solutions: Scalability Approaches
-
01
Layer 1 vs Layer 2 Blockchain Solutions: Scalability Approaches
Layer 1 vs Layer 2 Blockchain Solutions: Scalability Approaches
Introduction to Layered Scaling: L1 vs L2
Blockchain scalability presents a foundational challenge for widespread adoption: how to increase transaction throughput and reduce latency without compromising security or decentralization. Layer 1 solutions focus on the base protocol itself, while Layer 2 approaches build on top of an existing chain to move much of the load off the main settlement layer. For business-technical audiences, understanding this distinction helps in designing architectures that align with risk tolerance, regulatory requirements, and performance targets.
In practice, Layer 1 and Layer 2 strategies are not mutually exclusive. Enterprises often pursue a blended approach: upgrading the base chain to improve safety and throughput where feasible, while also deploying Layer 2 channels, rollups, or sidechains to meet specific user experience and cost objectives. This article outlines how each layer addresses scalability and how organizations can approach decision-making with a view toward resilience and long-term value.
Layer 1 Blockchains: Fundamentals and Examples
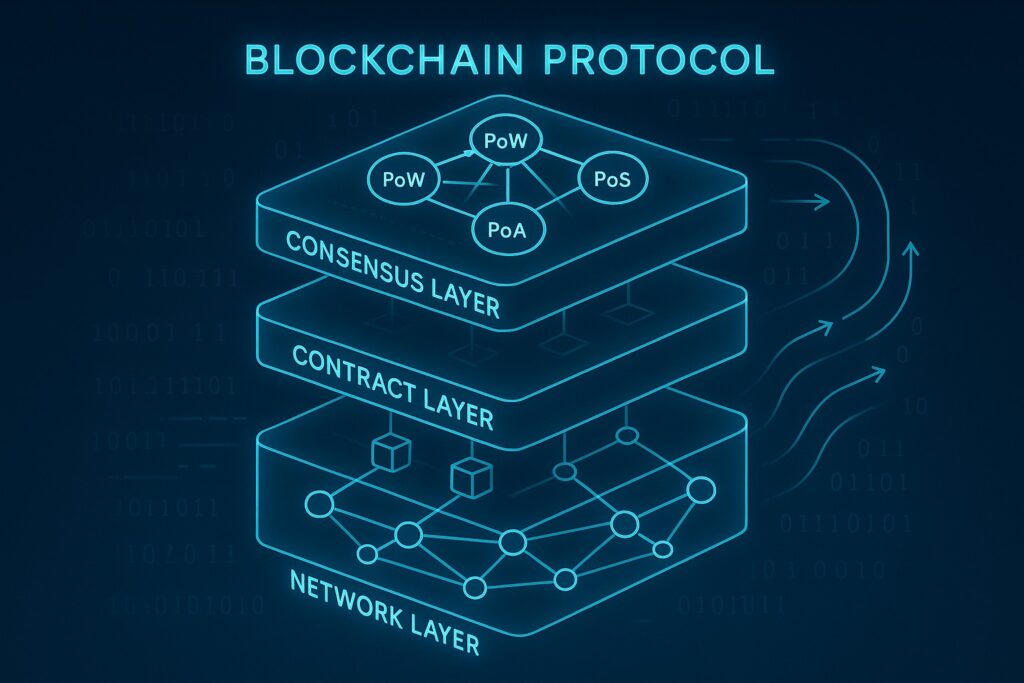
Layer 1 encompasses the underlying blockchain network—the protocol itself, including consensus rules, data availability, and finality guarantees. Improvements at this level aim to strengthen security, accelerate block processing, and widen the base layer’s capacity to handle more transactions per second. Because the settlement layer underpins all activity on the network, changes here often require broad coordination, protocol upgrades, and community consensus. Layer 1 upgrades tend to be more conservative in deployment but can yield substantial, lasting impacts on security and trust assumptions.
Key mechanisms used in Layer 1 design include protocol-level optimizations, sharding architectures, and consensus model refinements. To illustrate, a sharded Layer 1 architecture partitions network state so that different subsets of nodes process transactions in parallel, potentially multiplying throughput. Consensus upgrades may alter finality times or block production rules to reduce bottlenecks. Data availability improvements enhance the ability of nodes to verify and relay information quickly, which supports higher throughput without sacrificing decentralization. The following list summarizes representative features you may see in Layer 1 roadmaps:
- Enhanced throughput through parallel processing of transactions
- Modular consensus designs that can adapt to network growth
- Improvements in data availability and propagation speed
- Participation incentives that maintain decentralization at scale
- Interoperability standards enabling cross-chain asset transfers
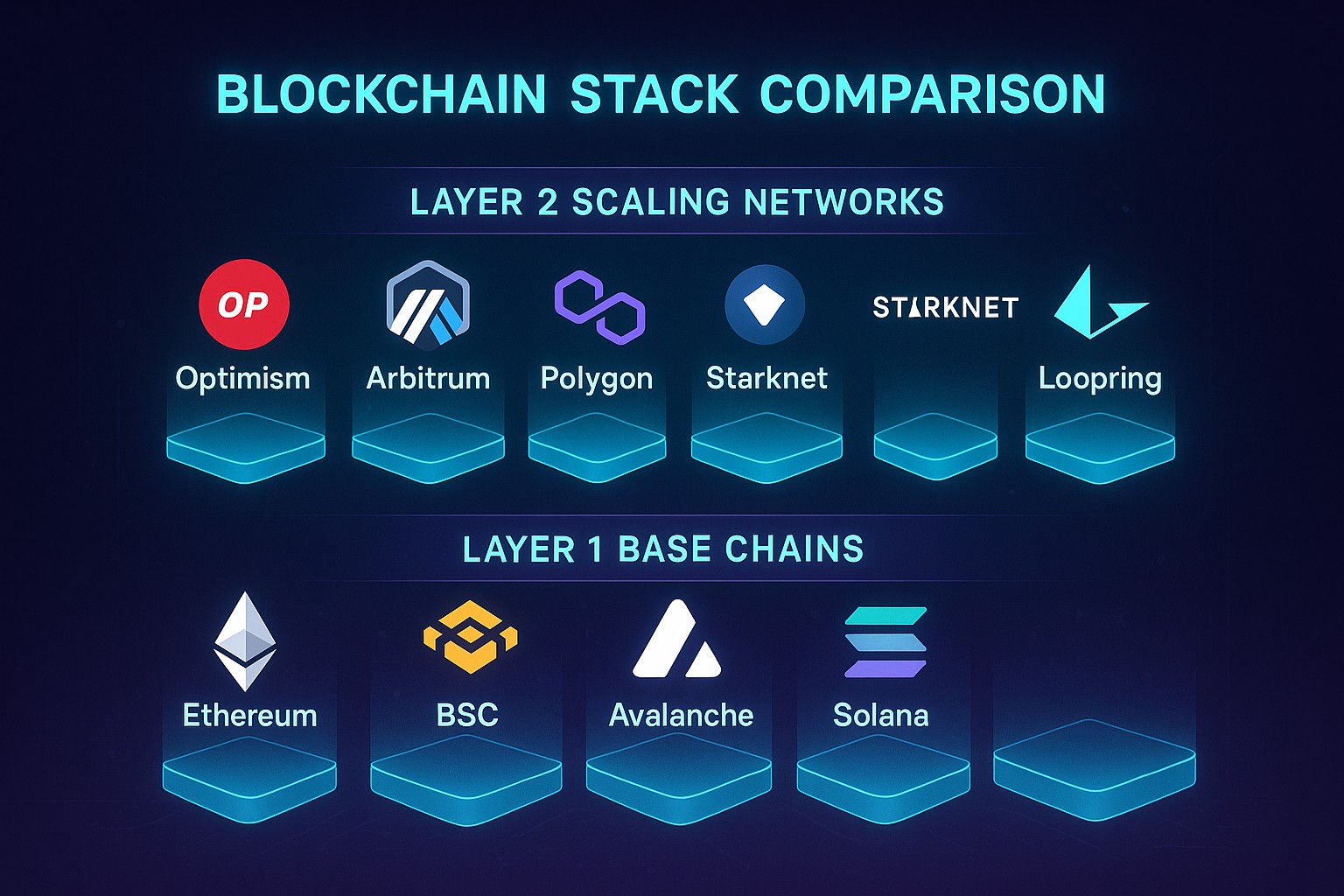
Layer 2 Solutions: Off-Chain Scaling and Their Mechanisms
Layer 2 refers to protocols and frameworks that operate atop an existing Layer 1 chain, taking on a portion of the transactional burden to improve speed and reduce fees. The core idea is to keep the security and finality of the base layer intact while moving the bulk of operations into secondary structures. Layer 2 technologies can deliver near-instant finality for many transactions, with disputes and settlements periodically anchored to the Layer 1 chain for ultimate security. This separation often results in a user experience that feels like a fast, private, or scalable system, while still anchoring trust to the mainnet.
Common Layer 2 approaches include state channels, optimistic and zero-knowledge rollups, and sidechains. State channels enable many off-chain interactions with periodic on-chain commitments, suitable for high-frequency use cases. Rollups compress and aggregate transaction data before posting to Layer 1, preserving security properties while sharply increasing throughput. Sidechains run parallel chains with their own security models, trading some degree of independence for flexibility and lower finality latency. The following list captures representative Layer 2 archetypes:
- State channels for fast, interactive sessions with off-chain dispute resolution
- Optimistic rollups that assume correctness until proven otherwise
- Zero-knowledge (zk) rollups that publish succinct proofs of correctness
- Sidechains with independent consensus and finality timelines
Comparative Analysis: Strengths and Weaknesses
Layer 1 upgrades offer stronger, long-horizon security and a more straightforward model for governance and risk management, but they can entail slower iteration cycles and higher capital expenditure for protocol changes. Layer 2 solutions provide rapid scalability gains, improved user experiences, and lower per-transaction costs, yet they introduce additional trust considerations, potential security trade-offs, and bridging mechanics that must be designed carefully. The choice between these layers often hinges on the application’s latency tolerance, regulatory posture, and the desired balance between decentralization and performance.
To help visualize how these layers differ along core dimensions, consider the following high-level comparison table. It distills the relative emphasis of each layer against key business metrics.
| Aspect | Layer 1 | Layer 2 |
|---|---|---|
| Security model | Unified security of the base chain; finality governed by protocol | Anchored to Layer 1 security; additional off-chain assumptions |
| Throughput potential | Limited by consensus and data availability constraints | Substantially higher throughput via off-chain processing |
| Latency and finality | Often slower finality due to block confirmation times | Near-instant finality in many use cases, with periodic Layer 1 settlement |
| Data availability | All data resides on-chain | Data can be off-chain or compressed with on-chain proofs |
| Cost per transaction | Higher baseline costs if throughput is constrained | Lower costs per transaction at scale through aggregation |
Security, Trust, and Finality Implications
Security guarantees are central to choosing between Layer 1 and Layer 2. Layer 1 provides the baseline trust model, where validators or miners secure the entire protocol and finality is determined by the consensus mechanism. Layer 2 inherits its security posture from Layer 1 but introduces additional assumptions—such as the reliability of fraud proofs in optimistic systems or the correctness of cryptographic proofs in zk-rollups. Enterprises must assess the risk that bridging assets between layers introduces, including potential bridge vulnerabilities, challenge windows, and liquidity dependencies.
Finality timelines and dispute resolution processes also guide architectural decisions. When ultra-fast confirmations are essential for user experience, Layer 2 can deliver the immediacy users expect, while occasional on-chain settlements preserve correctness and auditability. Governance is another dimension: Layer 1 upgrades are typically slower and require broad community consensus, whereas Layer 2 deployments may offer more agility but demand careful coordination with the Layer 1 security model to avoid misaligned incentives and fragmentation.
Developer Experience and Ecosystem Maturity
From a development perspective, Layer 1 ecosystems tend to emphasize long-term stability, with mature tooling and established security review processes. However, iteration cycles on Layer 1 can be slower due to protocol-wide consensus requirements and the need to maintain backward compatibility. Layer 2 environments often boast vibrant developer communities, faster feature rollouts, and modular tooling that accelerates experimentation. This dynamic can be highly appealing for startups and enterprises seeking to prototype new business models or product experiences quickly, provided they design robust interoperability with the Layer 1 chain.
Tooling, documentation, and testnet availability are essential to reducing time-to-market. For teams evaluating Layer 2, the trade-off is typically a richer feature set and improved UX against the need to manage bridging logic, security assumptions, and cross-layer monitoring. Adoption decisions should weigh not only technical capabilities but also alignment with internal skillsets, procurement processes, and partner ecosystems that can support on-going maintenance and compliance requirements.
Business and Strategical Considerations for Enterprises
Enterprises evaluating Layer 1 versus Layer 2 options must align architectural choices with cost structures, risk budgets, and regulatory expectations. Layer 1 upgrades can be attractive when the business model relies on strong, uniform security guarantees and long-term network health. Layer 2 solutions are compelling for applications requiring high throughput, low latency, and micro-transaction economies, such as retail payments, supply-chain tracking, or scalable tokenized services. The decision often rests on a combination of performance targets and risk appetite for cross-layer complexity.
To operationalize the decision, organizations should adopt a structured approach to vendor evaluation, security testing, and governance design. Considerations include how to handle liquidity provisioning across layers, how to monitor cross-layer state, and how to ensure data sovereignty and privacy. The following checklist highlights factors that frequently influence enterprise governance and procurement decisions:
- Security guarantees and audit readiness across layers
- Cost models, including setup, maintenance, and on-chain settlements
- Interoperability and standards alignment with existing systems
- Regulatory compliance and data governance implications
- Vendor risk, roadmaps, and support commitments
Roadmap to Adoption: When to Use Layer 1 versus Layer 2
Successful adoption typically starts with a clear mapping of business requirements to technical capabilities. If the priority is absolute security, base-layer finality, and minimal cross-layer risk, Layer 1 upgrades may be the most prudent path. For use cases demanding low latency, high throughput, and cost efficiency, Layer 2 deployments can unlock practical scalability without forcing a complete re-architecture of the settlement layer. A phased approach—beginning with a Layer 2 pilot while maintaining the option for Layer 1 upgrades—often yields the best balance of speed and resilience.
Key steps include establishing performance and risk targets, selecting compatible Layer 1 and Layer 2 technologies, and designing robust bridging and monitoring capabilities. Organizations should also plan for governance and rollback procedures in the event of integration issues, ensuring business continuity even in the face of cross-layer disputes or security incidents. Communication with stakeholders, including developers, operations, legal, and executive leadership, is essential to maintain alignment as the project progresses.
Implementation Challenges and Governance
Interoperability between Layers 1 and 2 introduces architectural complexity that requires careful design. Bridging assets between layers, cross-layer state verification, and consistent monitoring add surfaces for potential failure modes if not implemented with rigorous security and testing. Standardization efforts and common frameworks for cross-chain messaging and data proofs can mitigate risk, but organizations should still expect to invest in dedicated security reviews, formal testing, and contingency plans for edge cases.
Governance models for Layer 1 upgrades and Layer 2 deployments differ in pace and scope. Layer 1 often relies on broad consensus, with long-term roadmaps and stakeholder alignment across the ecosystem. Layer 2 governance may be more modular, with protocol-specific communities, operators, and auditors contributing to decision-making. Enterprises should design governance processes that accommodate these dynamics, including clear onboarding for new technical partners, transparent change-management protocols, and defined escalation paths for incident response.
FAQ
What is the primary difference between Layer 1 and Layer 2 in blockchain scalability?
The primary difference is where the scaling work happens. Layer 1 upgrades improve the base protocol itself to increase capacity and security, while Layer 2 solutions operate on top of Layer 1 to move most transactions off the main chain, improving speed and reducing costs while keeping settlement anchored to Layer 1.
When should a business prioritize Layer 1 upgrades over Layer 2 deployments?
Prioritize Layer 1 upgrades when the business requires strong, long-term security guarantees, robust decentralization, and a unified governance model. If the goal is rapid user-facing performance, lower fees, and high throughput for high-volume transactions, Layer 2 deployments are often the more practical choice, especially for pilot programs or consumer-facing apps.
What are the main risks associated with Layer 2 solutions?
Key risks include reliance on bridging mechanisms that connect Layer 2 to Layer 1, potential delays in dispute resolution, liquidity provisioning across layers, and the added complexity of maintaining cross-layer security guarantees. Users may also face longer withdrawal times when moving assets back to Layer 1 in some configurations.
How do Layer 2 solutions impact user experience and transaction costs?
Layer 2 solutions typically deliver faster transaction finality and much lower fees by aggregating and compressing data before settlement on Layer 1. This can create a smoother, cheaper user experience, particularly for microtransactions or high-frequency interactions, though it introduces additional steps for users who need to move assets between layers.
Can Layer 1 and Layer 2 be used together in a single architecture?
Yes. A common pattern is to deploy Layer 1 as the secure settlement layer while using Layer 2 to handle the bulk of transactions. The two layers communicate through secure bridges or proofs, allowing assets and state changes to be settled on Layer 1 while enabling faster, scalable operations on Layer 2.