Now Reading: Low-Code vs Traditional Development: Impact on Teams
-
01
Low-Code vs Traditional Development: Impact on Teams
Low-Code vs Traditional Development: Impact on Teams

Overview
Low-code and no-code platforms have moved from niche prototyping tools to mainstream enablers of digital delivery. They allow business analysts, product managers, and other non-developer stakeholders to participate directly in building apps, dashboards, automations, and workflows. These platforms provide visual modeling, prebuilt connectors, and declarative logic that translates to working software with minimal hand-coding. In many organizations, this shifts a portion of software development from the traditional IT department to cross-functional teams, enabling faster experimentation and closer alignment with business needs.
This article analyzes the impact of low-code/no-code platforms on teams and the broader software delivery process. It highlights the benefits, the inherent limitations, and the governance considerations that come with wider participation. We will discuss practical patterns for adoption, how to structure teams, and the trade-offs that influence decision-making in a business-technical context.
Benefits of Low-Code for Teams
The major benefits center on speed, participation, and alignment. With visual editors, reusable components, and integrated data connectors, teams can prototype, validate, and iterate much faster than through traditional hand coding alone. This accelerates time-to-market for new features and processes while reducing the friction of involving non-technical stakeholders in the delivery loop.
- Faster prototyping and delivery cycles that shorten feedback loops and enable rapid course corrections.
- Expanded participation across functional teams, enabling domain experts to contribute directly to solutions.
- Reduced IT backlog as business units take on routine, well-scoped developments with guardrails in place.
- Consistent UI patterns and reusable components that promote a cohesive user experience and faster maintenance.
- Lower barriers to experimentation, encouraging small, inexpensive experiments that can scale if successful.
However, to realize these benefits at scale, organizations must invest in governance, architectural guidance, and ongoing training. Without these enablers, the same speed advantages can give rise to fragmentation, operational risk, and inconsistent data practices.
Limitations and Trade-offs
Low-code and no-code approaches are powerful where the problem domain fits their capabilities, but they are not a universal solution. Some applications require deep customization, specialized performance optimizations, or complex integrations that push beyond what visual modeling can express. In these cases, traditional development or a carefully architected hybrid model often remains necessary.
Common limitations include constrained customization, potential vendor lock-in, and challenges around integrating with legacy systems or complex data models. Governance and security considerations become more pronounced as more teams participate in building and deploying software. In addition, large-scale usage can lead to a proliferation of independently developed apps, which complicates policy enforcement, data stewardship, and incident response. Recognizing these trade-offs helps leaders align platform choice with appropriate use cases, avoiding the risk of quick wins that become long-term liabilities.
Impact on Team Structure and Processes
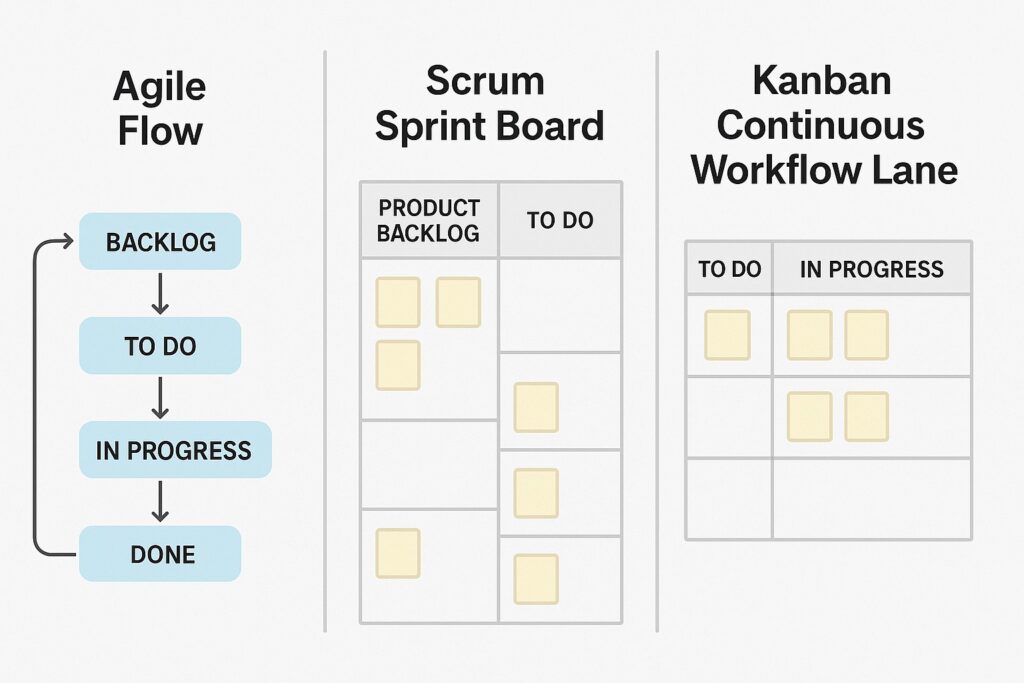
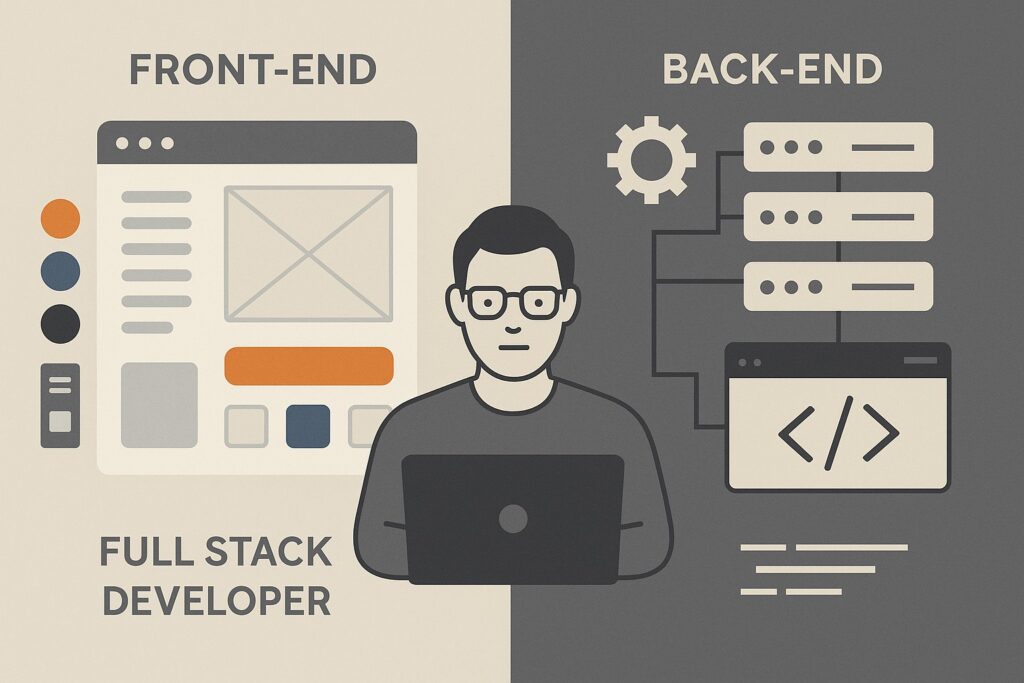
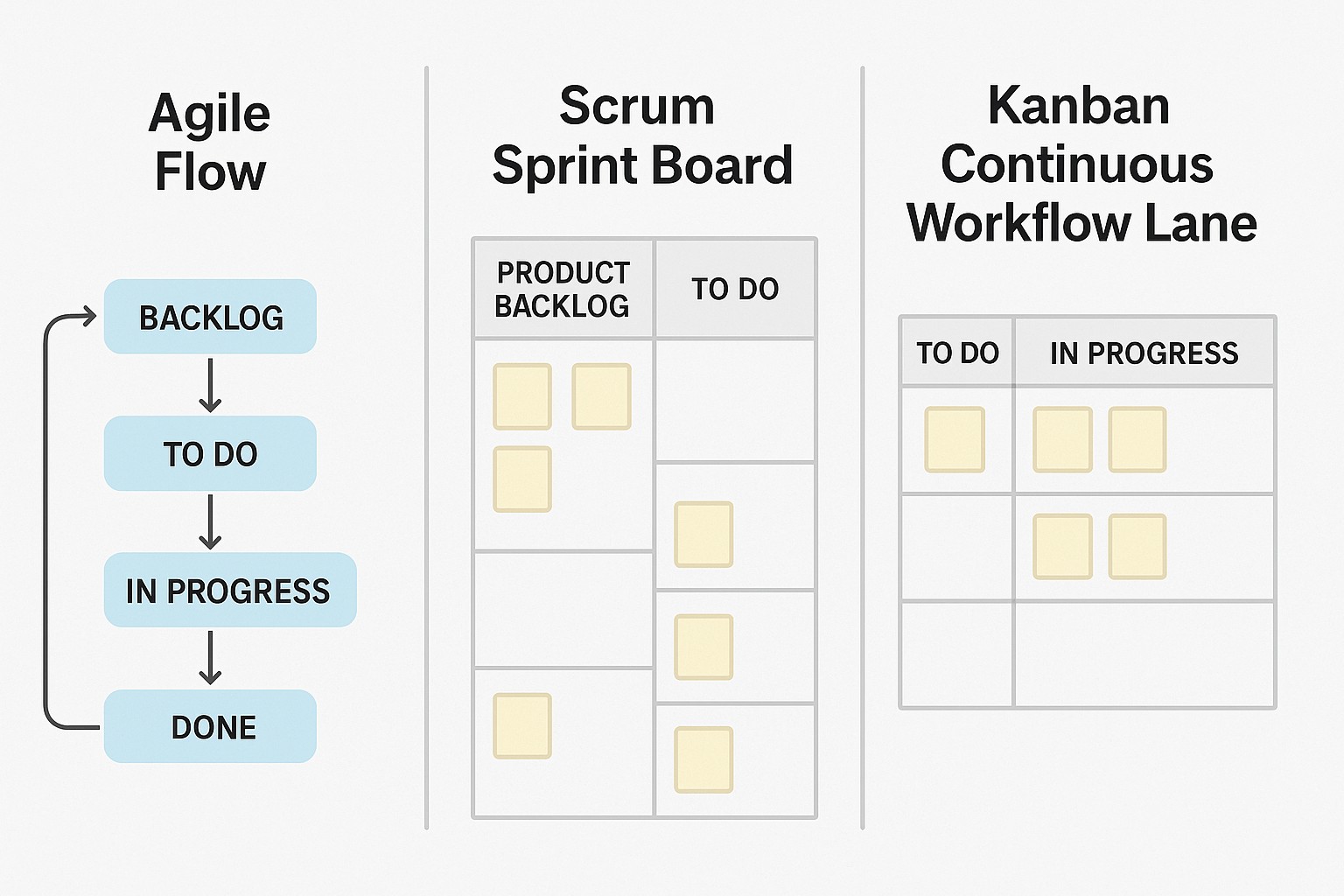
Adopting low-code/no-code platforms tends to reshape team composition and workflows. IT remains essential for governance, security, integration, and strategic direction, while business units gain empowerment to deliver solutions. This often results in new cross-functional roles, such as platform product owners, citizen developers, and shared services teams focused on component libraries and standardized patterns. The collaboration between IT and business units intensifies, requiring clear policies, shared roadmaps, and aligned metrics.
Process changes accompany this shift. Prioritization methods adapt to balance business value with risk, architecture reviews scale from project-level assessments to platform-level governance, and change-management practices emphasize training and adoption support. Organizations that succeed with this transformation typically implement a lightweight yet disciplined governance model, including guardrails for data access, security reviews, and documented patterns for common scenarios. When approached thoughtfully, these adjustments improve delivery speed without sacrificing reliability or control.
Practical Implementation Considerations
Realizing the benefits of low-code/no-code platforms requires deliberate planning and a structured approach to adoption. Start with clear objectives, select non-critical but high-value use cases, and establish a foundation of reusable components and guidelines. Align platform choices with your organization’s data strategy, security posture, and integration requirements to maximize long-term value and minimize risk.
- Security and compliance: define role-based access, data handling rules, and audit trails; ensure connections to data sources meet regulatory requirements.
- Interoperability and data integration: ensure the platform can connect to key systems, supports standard data models, and enables data consistency across apps.
- Scalability and performance: evaluate the platform’s ability to handle growing user bases, concurrent runs, and complex workflows without degradation.
- Vendor support and ecosystem: assess vendor roadmaps, community resources, and the availability of skilled practitioners in your region.
- Total cost of ownership: consider licensing, infrastructure, training, and potential hidden costs as adoption scales.
- Training and enablement: invest in onboarding programs, maintainable component libraries, and ongoing coaching for citizen developers.
Beyond these practical considerations, organizations should establish a governance model that includes a lightweight center of excellence, clearly defined roles and responsibilities, and decision protocols for when to reuse existing components versus create new ones. This helps maintain consistency, streamline support, and prevent fragmentation as more teams engage with the platform.
Adoption Strategy and Governance
A pragmatic adoption path begins with a focused pilot that targets a well-scoped, high-value process. Lessons learned from the pilot inform the rollout plan, including standardized patterns, security controls, and governance processes. As usage expands, you should formalize a platform roadmap, expand the library of reusable components, and implement governance checks at each stage gate—from ideation to production deployment.
Governance is not about bottlenecks; it is about enabling safe, scalable delivery. Establish a steering function that curates best practices, reviews critical integrations, and ensures alignment with data governance and security policies. Clarify ownership of platform assets, measure outcomes (speed, quality, user satisfaction), and continuously refine the set of recommended patterns and templates. A well-designed governance approach reduces risk while preserving the agility that low-code/no-code platforms are meant to unlock.
FAQ
How do low-code platforms affect software quality and governance?
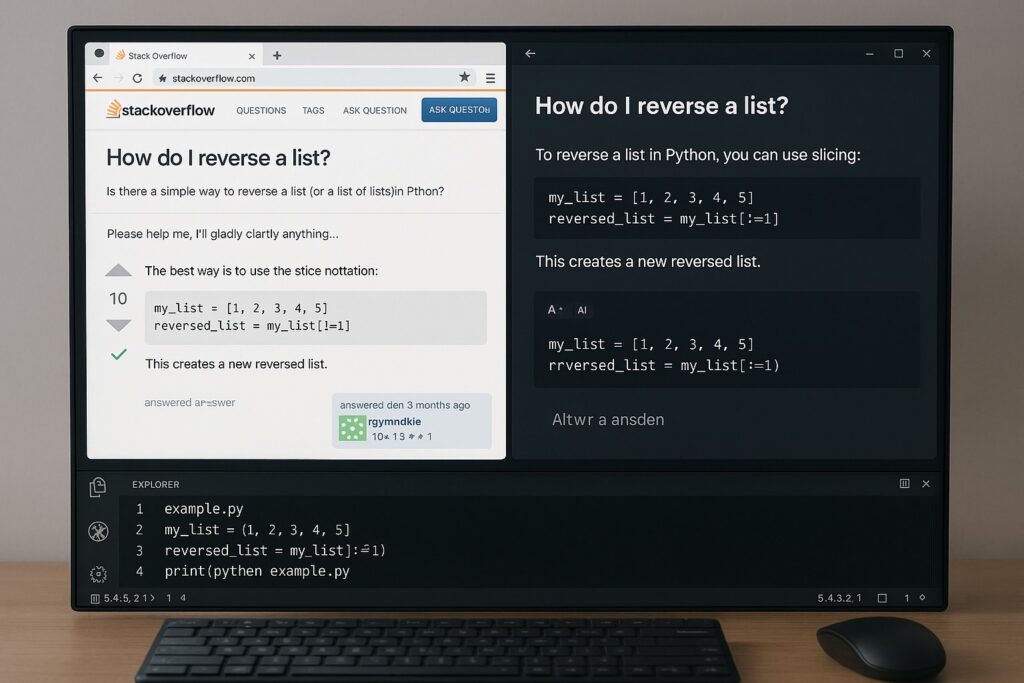
Quality and governance typically improve when organizations implement standardized components, explicit review gates, and clear ownership of platform assets. While citizen developers can accelerate delivery, governance ensures data integrity, security, and consistent architecture. Automated tests, code-free validation within the platform, and periodic audits help balance speed with reliability.
When should an organization choose low-code over traditional development?
Low-code is well suited for user-facing dashboards, workflow automation, internal tooling, and processes that require rapid iteration and frequent changes. It complements traditional development for core systems that demand deep customization, stringent performance requirements, and long-term strategic direction. A hybrid model often emerges as the most effective approach, aligning problem complexity with the appropriate delivery method.
What is the role of IT in a low-code/no-code environment?
IT typically acts as a steward of governance, security, data integrity, and integration strategy. IT provides guardrails, maintains the platform’s core infrastructure, reviews high-risk integrations, and helps scale best practices. At the same time, IT may partner with business units to develop reusable components and maintain a platform-wide catalog of approved templates.
How can teams mitigate risks of shadow IT and security concerns?
Mitigation involves explicit policy, transparent governance, and training. Establish a center of excellence to publish approved templates, enforce access controls, and require security reviews for new apps. Regular audits, centralized monitoring, and clear escalation paths for incidents help maintain control while preserving the benefits of broader participation.