Now Reading: DevOps vs DevSecOps: Adding Security to DevOps
-
01
DevOps vs DevSecOps: Adding Security to DevOps
DevOps vs DevSecOps: Adding Security to DevOps
Understanding DevOps and DevSecOps: Core Concepts
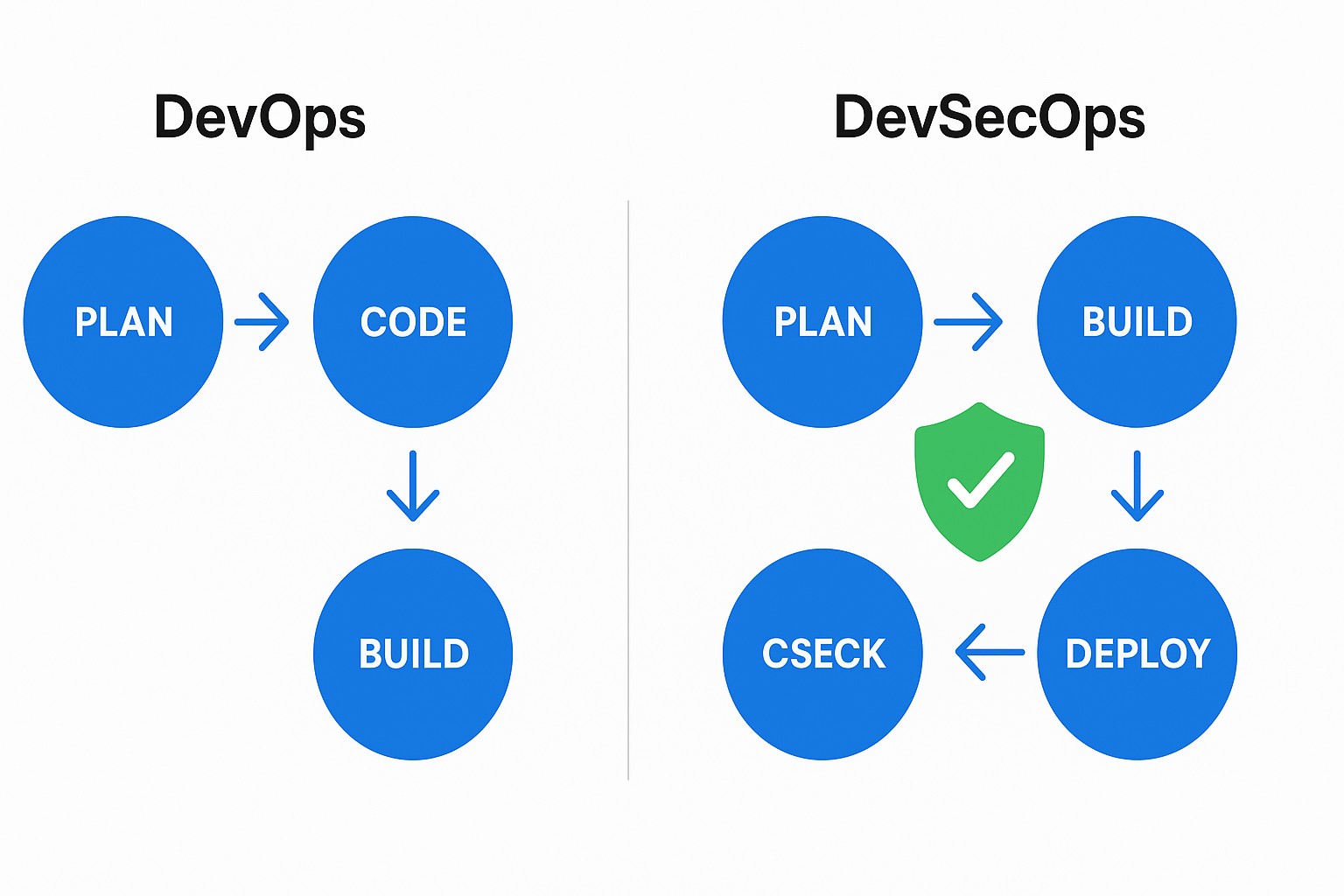
DevOps represents a cultural and technical shift designed to align development and operations teams around shared goals: faster delivery, higher quality software, and a sustainable velocity. It combines agile practices, automated testing, continuous integration and delivery, and a feedback loop that ties production insights back to the codebase. The outcome is not just faster releases, but a disciplined approach to risk management, collaboration, and reliability that scales with complex environments.
DevSecOps extends this foundation by placing security at the heart of the delivery pipeline, not as a gate that slows teams, but as an integrated practice that enables secure software at speed. Security becomes a shared responsibility across all roles, emphasizing automation, policy-as-code, and early risk assessment. The core idea is shift-left security: design, code, and pipeline decisions incorporate security requirements from the outset, reducing the cost and impact of remediation later in the lifecycle.
Security as a Priority: From Reactive to Proactive
In traditional models, security often operates in a separate phase, leading to late discoveries, patchwork fixes, and elevated risk during production. In a DevSecOps mindset, security is a proactive discipline embedded in every stage of the value stream. Teams practice threat modeling during design, integrate security testing into CI/CD, and implement controls that prevent insecure deployments by default. This shift lowers the probability of security incidents reaching customers and improves the organization’s ability to respond when issues arise.
To operationalize security, organizations rely on structured practices that make risk actionable for developers and operators. The following items capture essential activities that organizations typically adopt in a DevSecOps context:
- Secure design reviews and threat modeling integrated into early architecture decisions
- Automated vulnerability scanning and dependency management that runs in CI/CD
- Secrets management and robust access control across environments
- SLA-aligned incident response runbooks and automated alerting with prioritized remediation workflows
- Policy-as-code that codifies compliance and security controls
- Continual security education and security champions embedded in product teams
Observability and Automation in the Delivery Pipeline
Observability—covering logs, metrics, and traces—provides visibility into how software behaves in production and how security controls perform in real time. In a DevOps context, observability supports faster incident detection, better root-cause analysis, and more reliable deployments. In DevSecOps, observability extends to security signals: vulnerability trends, policy violations, encryption status, and access anomalies. The resulting data informs guardrails, prioritization, and continuous improvement across the pipeline, enabling teams to act on both performance and security risk with confidence.
Automation is the enabler that makes this approach scalable. By treating security and reliability as code, teams can repeat successful patterns, enforce guardrails, and recover quickly from failures. A typical automation pattern combines static analysis, dynamic testing, secret management, and deployment gates that enforce policy checks before promotion. The code example below illustrates a compact, automated sequence that many teams implement in their pipelines to enforce security checks without slowing delivery.
version: 1
name: DevSecOps Pipeline
on:
push:
branches: [ main ]
jobs:
build:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v3
- name: Static Analysis
run: run-security-scanner --fail-on-warn
- name: Dependency Check
run: check-dependencies --audit
- name: Secrets Scan
run: detect-secrets scan
- name: Deploy
if: github.event_name == 'push' && success()
run: deploy-prod
DevOps vs DevSecOps: Key Differences
The distinction between DevOps and DevSecOps is most evident in scope, responsibilities, and how risk is managed across the lifecycle. DevOps emphasizes rapid delivery, reliability, and collaboration between development and operations. DevSecOps expands that scope to include security as a first-class, automated, and continuously evolving component of every release. In practice, this means security is not a final checkpoint but an ongoing, auditable process integrated into design, code, build, test, and deployment.
In a mature DevSecOps environment, security practices influence architecture choices, tooling, and governance in ways that reduce rework and accelerate safe delivery. Teams adopt secure-by-default templates, automated policy checks, and secure configuration baselines. They also implement measurable security objectives, such as reduced mean time to remediate vulnerabilities, fewer high-risk findings in production, and demonstrable compliance with policy requirements without slowing development velocity.
Implementation Patterns and Best Practices
Adopting DevSecOps is a journey of people, processes, and technology working in harmony. A practical path emphasizes starting small, building guardrails, and scaling success across teams with a focus on reusability and clarity. Leadership support, clear ownership, and a culture of continuous learning are as important as the tooling and automation itself.
To guide implementation, organizations often rely on the following patterns that combine governance with practical execution:
- Define security and compliance requirements as code, so policies travel with the software and are enforced automatically in every environment
- Embed security champions in product teams who translate policy into practical engineering guidance and assistance
- Automate vulnerability management, secret handling, and configuration drift detection to minimize manual toil
- Create secure-by-default templates for infrastructure and application components to reduce surfacing of misconfigurations
- Instrument feedback loops through observability, incident postmortems, and continuous improvement cycles
Measurement and ROI: Security as a Business Driver
Measuring the impact of DevSecOps initiatives requires focusing on risk reduction as well as speed and cost. Traditional metrics like time to market or deployment frequency capture velocity, but security-minded leadership wants to see quantifiable improvements in risk posture, compliance readiness, and operational resilience. By combining observability data with security telemetry, teams can quantify the value of automation, the cost of remediation avoided, and the efficiency gains from policy-driven guardrails.
Common metrics to monitor include the rate of high-severity vulnerabilities remediated within agreed SLAs, the frequency of security-related failed deployments, the proportion of environments covered by automated tests, and the time from vulnerability disclosure to patch deployment. In practice these indicators help justify ongoing investment in secure-by-default templates, automated testing, and security training as essential capabilities that protect revenue, brand trust, and regulatory standing while maintaining competitive delivery speeds.
FAQ
What is the main difference between DevOps and DevSecOps?
The main difference is scope and focus: DevOps centers on accelerating delivery and improving collaboration between development and operations, while DevSecOps makes security a continuous, automated, and shared responsibility across the entire pipeline, from design to production, so security is integrated rather than bolted on.
How does security get automated in a DevSecOps pipeline?
Security becomes automated through policy-as-code, automated testing at every stage, secrets management, and guardrails that block insecure builds. This typically includes static analysis, dependency checks, vulnerability scanning, and compliance checks embedded in CI/CD, plus automated remediation workflows and real-time security observability.
What are common pitfalls when transitioning to DevSecOps?
Common pitfalls include treating security as a blocker rather than a facilitator, underestimating the cultural changes required, and implementing noisy alerts that overwhelm teams. Other risks involve misconfigurations in cloud environments, inadequate secret management, and a lack of ownership or incentives for secure design and incident response practices.
How do you measure ROI for DevSecOps initiatives?
ROI is best captured by risk-adjusted metrics alongside velocity. This includes reductions in time to remediate critical vulnerabilities, fewer production incidents, improved policy compliance, and cost savings from automated remediation, reduced rework, and a more predictable release cadence that still meets security requirements.