Now Reading: Penetration Testing vs Vulnerability Scanning: Key Differences
-
01
Penetration Testing vs Vulnerability Scanning: Key Differences
Penetration Testing vs Vulnerability Scanning: Key Differences
Overview: Penetration Testing vs Vulnerability Scanning
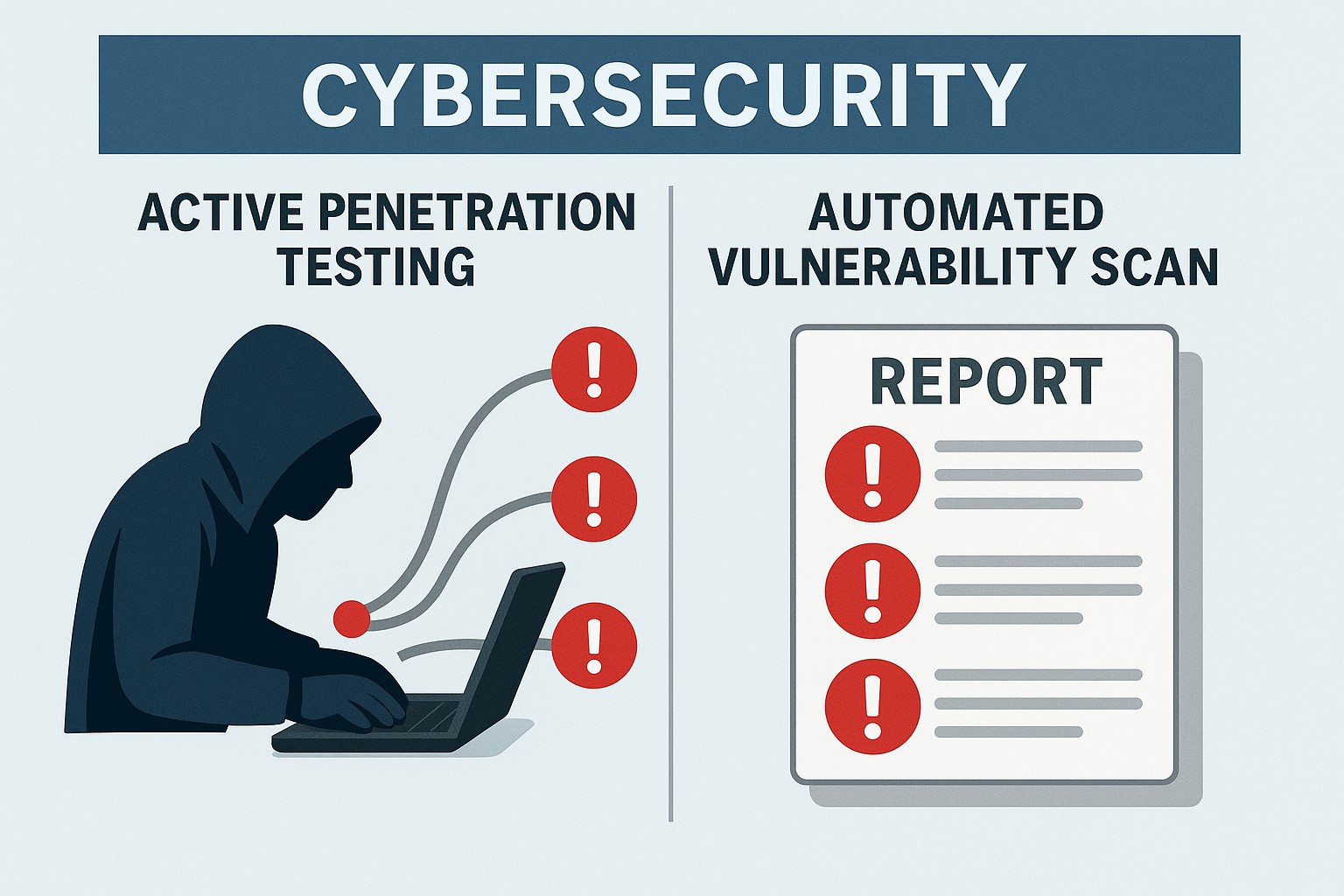
Penetration testing and vulnerability scanning are two pillars of a mature security program. They share a common objective—reducing risk by identifying weaknesses—but they differ in depth, methodology, and outcomes. Penetration testing simulates an attacker with defined authorization to exploit weaknesses, while vulnerability scanning is an automated process that inventories detectable issues across assets. Understanding how they complement each other helps executives align security investments with risk tolerance and regulatory requirements.
In practice, organizations use both approaches as part of a layered strategy. Vulnerability scanning often runs on a continuous or frequent cadence to surface new issues as systems change, while penetration testing is typically scheduled at strategic moments to validate critical control gaps and demonstrate real-world impact. The result is a more actionable view of risk, enabling prioritization of remediation efforts and tracking of progress over time. For many teams, this combination also helps satisfy governance expectations and supports evidence-based decision making in board rooms and compliance meetings.
Penetration Testing: what it is and how it works
Penetration testing, or pen testing, is a deliberate, authorized attempt to breach an organization’s defenses by exploiting vulnerabilities in systems, applications, and processes. Testers adopt attacker personas and follow a risk-based methodology to identify exploitable paths that could lead to data compromise, escalation of privileges, or disruption of operations. The goal is not merely to find flaws but to demonstrate their real-world impact under controlled conditions, with a clear path from discovery to remediation.
Typical engagements are scoped with business objectives in mind, and testers use a combination of manual techniques and automated tools. The process often includes information gathering, threat modeling, vulnerability validation, exploitation (in a safe, reversible manner), post-exploitation analysis, and a detailed report with prioritized remediation guidance. Deliverables emphasize business risk, with evidence of exploitability and concrete steps to close the gaps. In many programs, testers will also provide a risk-based remediation plan, including estimates of effort, potential controls, and suggested compensating controls where immediate remediation is not feasible.
Engagement types vary by depth and visibility. White-box testing provides testers with extensive access to architecture and code, black-box testing simulates external attackers with minimal prior knowledge, and gray-box testing blends both. Regardless of type, successful pen tests require clear authorization, well-defined scope, and management oversight to ensure operational continuity and legal compliance. Practical considerations include test windows that minimize disruption, data handling and privacy safeguards, and secure reporting channels for sensitive findings.
Vulnerability Scanning: what it is and how it works
Vulnerability scanning is an automated, typically ongoing process that inventories known security weaknesses across assets, including operating systems, applications, and network devices. Scanners compare observed configurations and software versions against published vulnerability databases and configuration baselines, producing a prioritized list of issues that merit attention. The emphasis is broad coverage and repeatable detection rather than active exploitation.
Scans can run with or without credentials and can be scheduled daily, weekly, or after major changes. Credentialed scans tend to provide deeper visibility into internal configurations and patch status, while non-credentialed scans are useful for external-facing perspectives. However, scanners can generate false positives and may miss context such as compensating controls, so results require triage and validation before remediation decisions are made. Effective vulnerability scanning also depends on accurate asset discovery, proper baselining, and regular refinement of scanning rules to reflect evolving technologies and threat landscapes.
Outputs from vulnerability scanning commonly include a consolidated risk score, asset inventory, affected components, and suggested remediation steps. They serve as a foundation for ongoing monitoring, vulnerability management workflows, and compliance reporting, especially when combined with patch management and change control processes. Many programs integrate scan results into ticketing systems, assign owners, and track remediation progress to closure as part of a mature cyber risk program.
Key differences between penetration testing and vulnerability scanning
While both activities aim to reduce risk, they operate at different depths and with different end goals. Penetration testing focuses on validating whether an attacker could move from a foothold to a meaningful impact, whereas vulnerability scanning focuses on identifying a broad set of weaknesses that could be exploited. The outcomes are complementary: pen tests reveal practical risk, while scans provide a living inventory that informs ongoing hygiene and patching efforts. In executive terms, pen tests demonstrate real-world attack feasibility, while scans quantify known vulnerabilities and their potential exposure across the estate.
- Goal and focus: simulated attacker scenario and impact validation vs automated detection of known weaknesses.
- Depth of testing: hands-on exploitation and privilege escalation in a controlled run vs broad, automated checks across many systems.
- Scope and cadence: time-bound, risk-based engagements with explicit rules of engagement vs continuous or scheduled scanning across the environment.
- Output and evidence: proof-of-exploit, risk prioritization, and remediation guidance vs vulnerability lists with severity, asset context, and patch status.
- Validation vs discovery: real-world exploitation demonstrations vs detection of potential issues only.
- Regulatory and governance alignment: many frameworks require both accurate asset inventories and validated risk scenarios, which benefits from both approaches.
Together, these approaches enable organizations to validate security controls in practice while preserving a real-time view of the vulnerability landscape. This dual perspective supports informed risk decisions, better resource allocation, and clearer communication with stakeholders about actual exposure and progress over time.
When to use Penetration Testing vs Vulnerability Scanning in a security program
Choosing when to perform a pen test vs a vulnerability scan depends on risk posture, regulatory requirements, and the pace of change in the environment. A well-rounded security program uses both, but the timing of each activity should reflect business priorities and operational realities.
Organizations typically rely on vulnerability scanning as a baseline practice and schedule penetration tests at strategic moments such as annual planning cycles, after major architectural changes, before product launches, or when new data classes are introduced. The cadence and scope should reflect the sensitivity of assets, the likelihood of exploitation, and the potential business impact of a breach. In dynamic environments, a combined cadence—regular scans plus targeted tests around high-risk changes—tends to yield the strongest risk signal for leadership and auditors alike.
- Regulatory and contractual requirements that mandate periodic testing or specific test types.
- Recent or planned changes to critical infrastructure, identity and access controls, or application code.
- The organization’s risk tolerance and appetite for demonstrated risk vs. ongoing hygiene.
- Resource availability and cost considerations, balanced with the need for actionable remediation guidance.
Best practices for integrating both into a security program
To maximize value, align testing activities with governance processes, asset management, and remediation workflows. This section outlines practical practices that help ensure results translate into measurable risk reduction.
- Coordinate testing with change management and patch cycles to minimize operational disruption and ensure findings remain relevant.
- Establish clear scoping, authorization, and escalation paths so both pen testers and scanners operate within approved boundaries and report incidents responsibly.
- Integrate findings into a centralized vulnerability management program with risk scoring, ticketing, and verification of remediation effectiveness.
Beyond the mechanics, successful programs invest in people, process, and tooling alignment. This includes training staff to interpret findings consistently, dedicating ownership for remediation, and maintaining a dashboard that ties technical outcomes to business impact. When leadership can see how risk levels shift in response to fixes and how regulatory requirements are being met, security becomes a measurable driver of business resilience rather than an abstract obligation.
Practical implementation considerations
In planning tests, map coverage to critical assets, data flows, and regulatory scope. Define success criteria, acceptance tests, and a remediation SLA to ensure findings are addressed in a timely manner. Consider resource constraints, third-party risk, and the need for coordination with operations to minimize business impact. Establish clear data handling policies for sensitive findings and ensure testers sign appropriate non-disclosure and privacy agreements before access is granted.
For ongoing vulnerability management, integrate scanning results with your asset inventory, configuration baselines, and patch management. Establish a repeatable workflow for triage, risk prioritization, remediation verification, and reporting to executive stakeholders. Regularly recalibrate risk scoring metrics to reflect evolving threats and changes in business priorities, and ensure remediation verification tests confirm that fixes are effective in production contexts.
Conclusion
Penetration testing and vulnerability scanning are distinct but complementary pillars of an effective security program. By combining realistic attack simulations with continuous visibility, organizations gain a clearer view of risk, the ability to prioritize fixes, and the evidence needed to demonstrate due diligence to leadership, customers, and regulators. The best security programs treat these activities as ongoing processes embedded in governance, technology, and culture rather than one-off events. When properly integrated, they enable smarter investments, faster remediation, and stronger confidence that security controls align with strategic business objectives.
FAQ
What is the primary difference between penetration testing and vulnerability scanning?
Penetration testing simulates an attacker to determine if flaws can be exploited to achieve a meaningful impact, often including controlled exploitation and post-exploit analysis. Vulnerability scanning automatically inventories known weaknesses across assets and provides a prioritized list of issues for remediation without attempting exploitation.
How often should vulnerability scanning be performed?
Vulnerability scanning is typically run on a frequent, automated cadence—daily, weekly, or after significant changes—to maintain an up-to-date view of the risk landscape. For many organizations, credentialed scans offer deeper visibility and are run as part of regular vulnerability management programs.
When is a penetration test most valuable?
A penetration test is most valuable when you need validated evidence of exploit paths, test critical business processes, or assess the effectiveness of security controls after major changes, such as a new application deployment, data migration, or cloud adoption. It is often scheduled to align with annual risk reviews or before strategic releases.
How should findings from both activities be integrated into risk management?
Findings should feed a centralized risk register, with clear ownership, remediation timelines, and verification steps. Prioritize based on business impact, data sensitivity, and threat likelihood, and track verification of fixes to close the loop.