Now Reading: Hybrid Cloud vs Multi-Cloud: What’s the Difference?
-
01
Hybrid Cloud vs Multi-Cloud: What’s the Difference?
Hybrid Cloud vs Multi-Cloud: What’s the Difference?

Overview: Hybrid Cloud and Multi-Cloud—Core Definitions
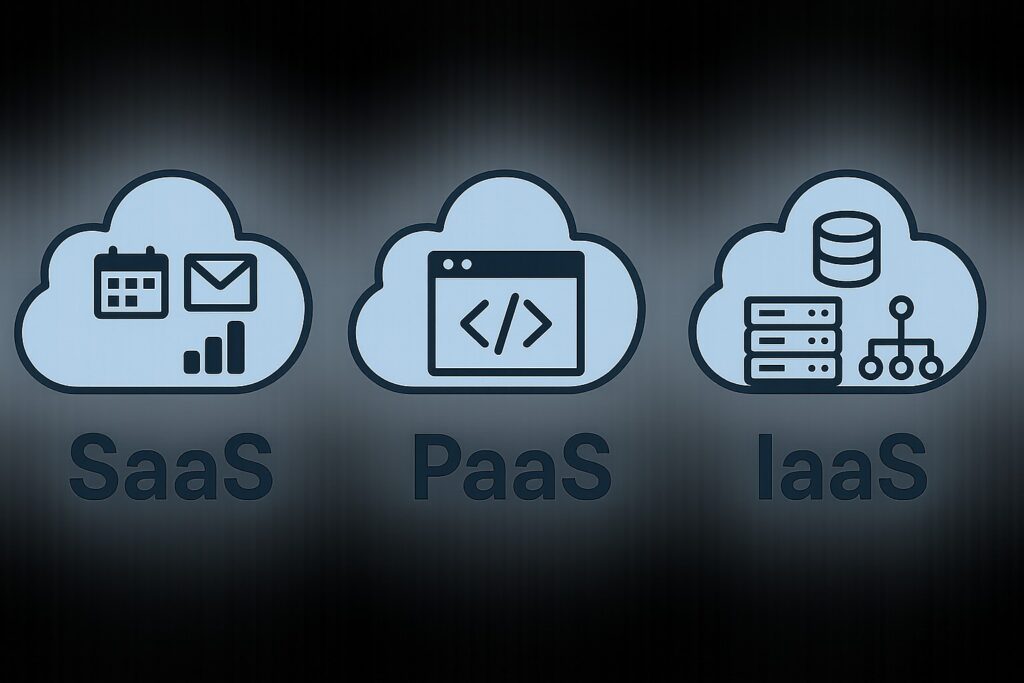
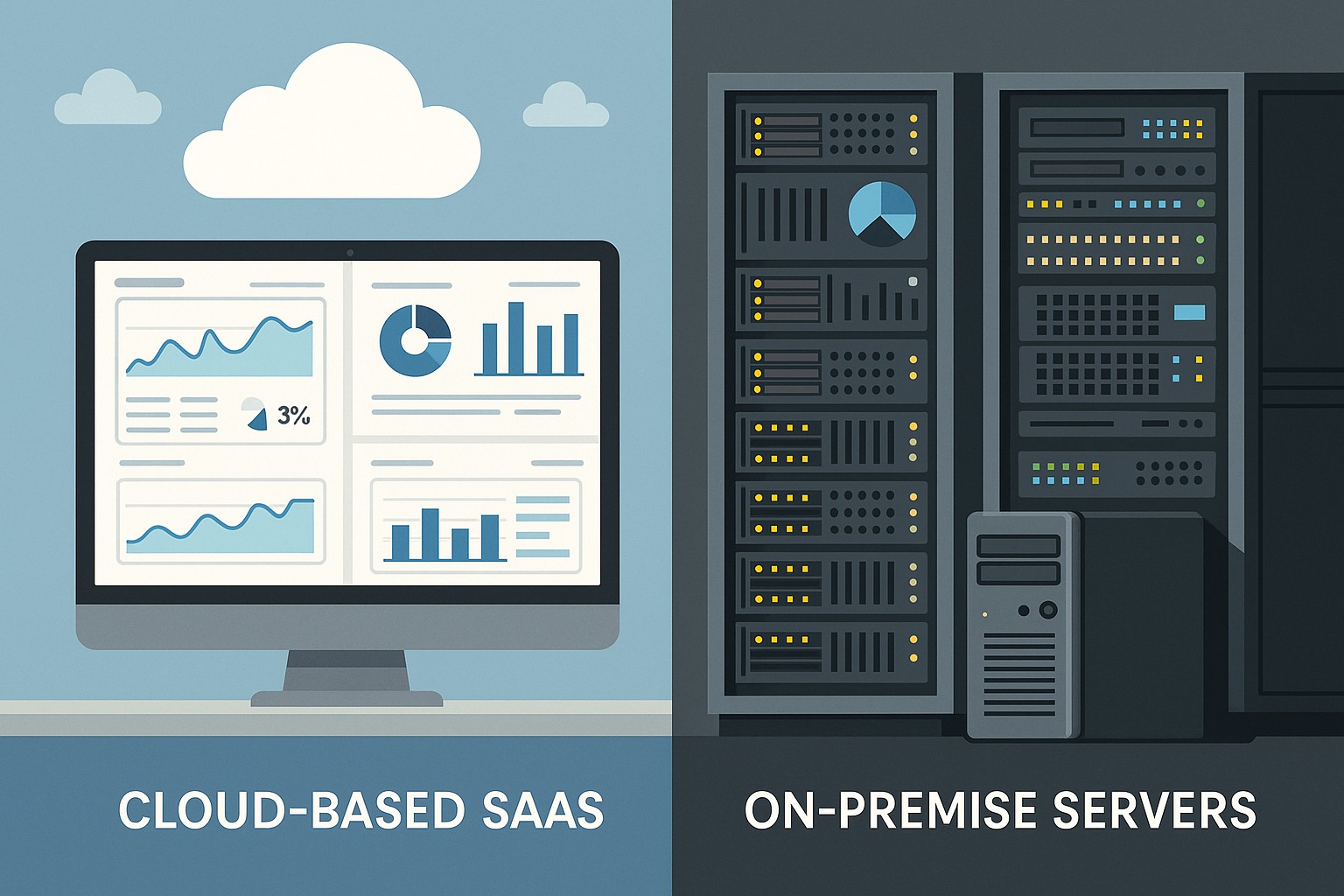
In modern IT strategy, the terms hybrid cloud and multi-cloud are frequently used in conversations about enterprise cloud adoption. While both approaches involve leveraging more than one cloud environment, they describe different architectural goals and governance challenges. In a hybrid cloud, organizations blend private infrastructure—often on-premises or in a private cloud—with public cloud services, aiming to create a unified environment that moves workloads across boundaries. In a multi-cloud model, an organization uses more than one public cloud provider to run workloads, often to capitalize on best-of-breed services or to mitigate provider-specific risks. The distinction matters because it shapes design choices, data management, and how you measure success. For many teams, the phrase cloud provider security comparison should be a central consideration as they map security controls and compliance requirements across diverse environments.
Understanding these definitions helps set expectations for complexity, governance, and cost. Hybrid cloud emphasizes seamless orchestration between on-premises and public resources, along with consistent policy enforcement and data placement decisions. Multi-cloud emphasizes interoperability and portability across distinct public clouds, with attention to API compatibility, credential management, and avoiding vendor lock-in. The difference is not merely semantic; it drives how you plan architecture, operations, and supplier relationships in ways that align with business objectives and risk tolerance.
What Hybrid Cloud Means
Hybrid cloud describes a deployment where a private computing environment is integrated with one or more public cloud services to support workloads, data, and services that require flexibility, scale, or resilience beyond what private infrastructure alone can deliver. The private side may run on a traditional data center, a private cloud, or a managed private environment, while the public side can be any major cloud provider. The aim is to create an integrated platform where workloads can move or access resources across boundaries in a controlled fashion.
In practice, hybrid cloud often centers on consistent policy enforcement, centralized identity, and standardized automation to ensure that a common set of governance rules applies regardless of where a workload runs. This approach supports scenarios like burst capacity for seasonal demand, disaster recovery with site failover, and data residency requirements that restrict certain data to a private or regulated environment. Because the private and public elements share a common management canvas, organizations can optimize for performance, latency, and compliance without ripping out existing investments.
What Multi-Cloud Means
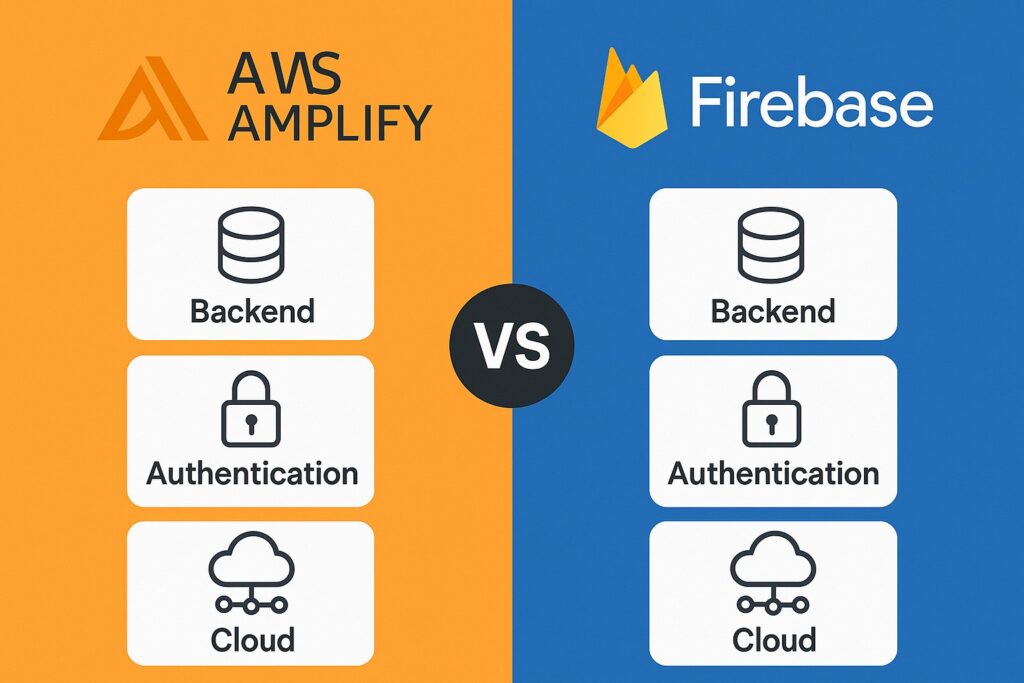
Multi-cloud refers to the use of multiple public cloud providers to run different workloads or services. The key characteristic is diversity—no single vendor handles the entire workload across all functions. Organizations may select a specific provider for compute, another for data warehousing, and a third for AI/ML capabilities, aiming to optimize for cost, performance, regional availability, or feature parity. Multi-cloud can reduce dependence on a single vendor and create opportunities to exploit best-in-class tools from different ecosystems.
Operationally, multi-cloud introduces complexity in areas such as identity and access management, API compatibility, data movement, and inter-cloud networking. To succeed, teams often implement a common automation layer, standardized security controls, and clear workload ownership. The approach can be more responsive to regional data sovereignty needs or regulatory variations, and it can provide resilience by avoiding a single point of failure across a single provider’s outage. The trade-off is higher coordination overhead, more diverse tooling, and the need for robust interoperability strategies.
Key Differences and How to Choose
The central distinction between hybrid cloud and multi-cloud lies in the scope of integration and the role of private infrastructure. Hybrid cloud centers on creating a single, coordinated environment that blends on-premises or private resources with public cloud services, emphasizing seamless data sharing, policy consistency, and a unified management plane. Multi-cloud, by contrast, emphasizes distributing workloads across multiple public clouds to maximize provider-specific advantages and minimize vendor risk, often with less emphasis on tightly coupling private infrastructure into the mix.
When choosing between these strategies, organizations should weigh governance maturity, data gravity, latency tolerances, and the skill sets available in the team. If workloads demand strict data residency, unified security controls across a private core and public edge, or a single management interface, a hybrid approach may be more appropriate. If the objective is to diversify providers to optimize capabilities and negotiate better terms, a multi-cloud approach can be advantageous. The decision is not binary; many enterprises adopt ahybrid multi-cloud pattern, where a hybrid backbone ties private resources to one or more public clouds while different clouds host specialized workloads or regional deployments.
Common Use Cases and Scenarios
Across industries, several patterns recurs when evaluating hybrid versus multi-cloud deployments. The choice often aligns with regulatory requirements, performance constraints, and the need for specialized cloud services.
Common use cases include:
- Seasonal or unpredictable demand where private infrastructure provides baseline capacity and public clouds supply elastic bursts.
- Disaster recovery and business continuity plans that rely on failover to a public cloud while maintaining primary workloads in a private data center.
- Data residency or sovereignty scenarios that require sensitive data to remain within a private or constrained region, with certain analytics or machine learning tasks offloaded to public clouds.
- De-risking vendor lock-in by spreading workloads across multiple clouds to preserve negotiating leverage and access to best-in-class capabilities.
- Leveraging specialized cloud services (such as AI/ML tooling, analytics, or edge compute) in a multi-cloud strategy while keeping core workloads in a controlled hybrid environment.
Architecture, Integration, and Data Management
Designing hybrid or multi-cloud architectures requires careful planning around data placement, API compatibility, and network topology. A hybrid approach often relies on a consistent control plane for policy enforcement, identity, and automation, with data that may traverse the private-public boundary. In a multi-cloud scenario, the emphasis shifts toward interoperability, standardized interfaces, and portable workloads that can move between clouds as needed.
To illustrate how these considerations map to architectural choices, the table below highlights typical alignment decisions for each model. The goal is to provide a concise lens on what each approach prioritizes in practice:
| Aspect | Hybrid Cloud | Multi-Cloud |
|---|---|---|
| Data governance | Unified policies across private and public environments; data mounting and residency rules are central. | Policies per provider with a cross-cloud governance layer; data movement requires explicit controls. |
| Security model | Consistent identity, access, and encryption across boundaries with a shared key management strategy. | Provider-specific controls complemented by a common security framework and centralized auditing. |
| Networking | Tightly integrated network connectivity between on-premises and cloud resources; latency considerations drive design. | Inter-cloud networking with optimized data paths and service chaining across providers. |
| Operations | Single ecosystem with a unified management plane; hybrid automation patterns are common. | Distributed management across providers; standardized tooling and agent parity are critical. |
Security and Compliance Considerations
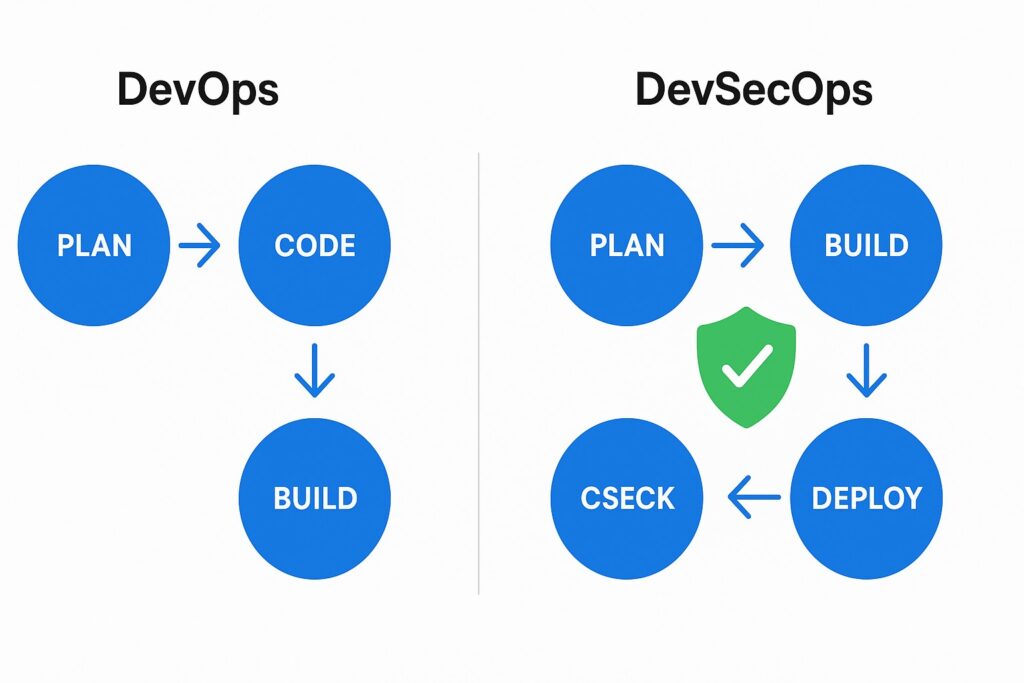
Security in hybrid and multi-cloud deployments requires translating policy into enforceable controls across diverse environments. A core objective is to maintain consistent identity, encryption, and access management so that users and services operate under the same security expectations, regardless of where they run. This often entails a centralized identity provider, a unified key management approach, and automation that enforces security baselines at every layer—from network segmentation to application configuration.
Compliance obligations add another layer of complexity, as different jurisdictions may demand data locality, auditability, and retention rules. Planning for data minimization, secure data transfer, and continuous monitoring helps organizations maintain a strong security posture. In practice, many teams perform a cloud provider security comparison as part of due diligence to ensure that controls align with internal risk appetite and external regulatory requirements. The outcome is a roadmap for consistent controls, transparent reporting, and auditable evidence across private and public resources.
Cost, Procurement, and Vendor Considerations
Cost models for hybrid and multi-cloud environments differ markedly. Hybrid strategies often revolve around optimizing utilization of private infrastructure with on-demand bursts in public clouds, balancing capital expenditure with operating expenditure. Multi-cloud approaches tend to emphasize rate cards, data transfer costs, and service-level differences across providers, with attention to avoiding hidden expenses in data egress and API calls. A disciplined procurement strategy combines total cost of ownership analysis with long-term flexibility and risk profiling.
When selecting providers, organizations assess not only price but feature parity, support quality, geographic reach, and compatibility with existing tooling and processes. A practical approach is to map workloads to the provider that offers the best fit for each capability, while maintaining a framework that enables rapid migration if requirements shift. This often requires governance around shadow IT avoidance, standardized interfaces, and a clear escalation path for vendor-related issues. A well-defined procurement playbook helps ensure that the arrangement remains aligned with business goals and can adapt to changing technology and regulatory landscapes.
Implementation Patterns and Best Practices
Adopting either a hybrid or multi-cloud strategy benefits from a structured blueprint that reduces risk and accelerates value delivery. While every organization has its own constraints, several patterns recur across successful implementations. Establishing a robust governance model, aligning security with policy as code, and ensuring automated, auditable operations are foundational elements.
To guide execution, follow a disciplined sequence that combines people, process, and technology. The steps below provide a practical path from design to operations:
- Define a clear business objective for either a hybrid or multi-cloud approach, with measurable success criteria and risk tolerance.
- Consolidate identity and access management to a single source of truth, then extend policy through automation across all environments.
- Adopt a common instrumentation layer for monitoring, logging, and alerting that aggregates signals from private and public clouds into a single dashboard.
- Standardize deployment automation, configuration management, and IaC (infrastructure as code) patterns to reduce drift and improve reproducibility.
- Implement a formal change-management and cost-control process that accounts for cross-cloud dependencies, data transfer, and service-level commitments.
FAQ
What is the main difference between hybrid cloud and multi-cloud?
The main difference is architectural intent: hybrid cloud combines private infrastructure with public cloud services to create a unified environment, whereas multi-cloud uses multiple public cloud providers to run workloads independently or with selective integration. Hybrid emphasizes seamless workload mobility and consistent governance across private and public resources; multi-cloud emphasizes diversification of providers to access best-in-class services and reduce dependency on a single vendor.
Which model is best for regulated industries?
Regulated industries often benefit from hybrid configurations when data residency and strict control over the private core are essential, paired with selective public cloud usage for non-sensitive workloads. However, a well-governed multi-cloud approach can also support regulatory compliance by allowing workloads to be placed in the most compliant region or provider while maintaining auditable controls and policy enforcement across clouds. The right choice depends on the specific regulatory landscape, data flows, and the ability to implement consistent security and governance across environments.
How do you manage security across multiple clouds?
Managing security across multiple clouds typically requires a centralized security framework that enforces identity, access control, encryption, and monitoring across all environments. This includes a single identity provider, consistent encryption keys with a centralized key management system, policy-as-code for automated enforcement, and cross-cloud visibility through unified security telemetry. Regular security assessments, shared incident response playbooks, and consistent configuration baselines are essential to reduce gaps created by disparate cloud footprints.
What are the common challenges and how to mitigate them?
Common challenges include increased operational complexity, data gravity, inconsistent tooling, and potential cost inflation from data transfer between environments. Mitigation strategies involve establishing a governance model with clear ownership, adopting standardized interfaces and automation, implementing a centralized observability platform, and performing ongoing cost optimization analyses. Early stakeholder alignment on objectives, metrics, and risk tolerance helps prevent scope creep and ensures the chosen strategy delivers tangible business value.
What roadmap should organizations follow when considering hybrid vs multi-cloud?
A practical roadmap starts with a business-driven assessment of objectives, regulatory constraints, and risk appetite, followed by a technology landscape review to map workloads to the appropriate environment. Build a governance and security foundation with policy as code and identity management, then pilot with a small set of workloads to validate orchestration, data movement, and monitoring. Scale gradually, refining cost models and aligning procurement with evolving requirements, before committing to a broad, organization-wide deployment that aligns with the broader digital transformation strategy.